Your cart is currently empty!
Category: Privacy & Security
-

Cybersecurity Insights: From Police Officer to CISO Transition
Explore the CISO Experience: Navigate the Evolving Cybersecurity Landscape
Welcome to the second episode of Series 3 of the CISO Experience, currently streaming live on the Infosec Live channel. This captivating series delves into authentic discussions with leading security experts, focusing on the technological advancements, human factors, challenges, and emerging opportunities that are reshaping the cybersecurity landscape. Our sponsor, Simple Security, champions the idea that cybersecurity doesn’t have to be overly complex. They are dedicated to delivering enterprise-level security solutions that are both accessible and affordable for businesses of all sizes and sectors, ensuring everyone can protect their digital assets effectively.
Discover Adam Pilton’s Inspiring Journey from Law Enforcement to Cybersecurity Expert

Today, we are excited to feature Adam Pilton, a dedicated cybersecurity professional whose career began in 2016. Adam’s story is both motivating and educational, as he transitioned from cybercrime investigation to advisory positions. His distinctive viewpoint fuses technical proficiency with hands-on application, enabling him to simplify intricate risks into actionable strategies for business executives. This approach significantly enhances their understanding of cybersecurity protocols and practices, ultimately empowering them to make informed decisions regarding their security posture.
Key Lessons from Adam’s Law Enforcement Career that Shaped His Cybersecurity Perspective
Adam embarked on his professional journey as a police officer, dedicating 15 impactful years to this role. He was at the forefront of the covert operations unit, which encompassed three specialized teams: the Covert Authorities Bureau, Communications Data Investigators, and the Cybercrime Team. His responsibilities included securing lawful authorities for covert operations, addressing issues spanning both physical and digital domains, thus providing him with a comprehensive understanding of crime in both spheres.
One of the most significant insights Adam gained from his early career experiences was the deep human impact of cyber threats. He interacted with victims, both individuals and organizations, witnessing firsthand the devastating consequences of cybercrime. For instance, losing access to a Facebook account may initially seem trivial; however, if it contains irreplaceable memories such as photographs of loved ones, the emotional fallout can be profound and enduring, highlighting the personal stakes involved in cybersecurity.
Strategic Career Move: Adam’s Successful Transition to the Private Sector
After 15 rewarding years in law enforcement, Adam recognized that he had reached the peak of his career. The limited opportunities for advancing his team’s digital capabilities, combined with the allure of frontline roles, prompted him to leave the police service. He subsequently joined Heimdal Security, attracted by their high-quality products and the chance to continue making a significant impact in the field of cybersecurity, thus embracing a new chapter in his professional journey.
Understanding the Cybersecurity Landscape: Challenges and the Need for Proactive Measures

Adam argues that the cybersecurity sector is facing a significant motivation dilemma. Despite constant media coverage highlighting various cyber threats, many organizations acknowledge the urgency for immediate action yet struggle to implement effective solutions. The overwhelming complexity associated with cybersecurity often leaves companies unsure of where to begin their improvement journey, creating a barrier to effective security enhancement.
To address this critical issue, Adam advocates for the adoption of structured frameworks like Cyber Essentials in the UK. These frameworks offer a clear roadmap for organizations to enhance their cybersecurity measures, enabling them to implement fundamental practices while progressively improving their capabilities. A recent study discovered that 60% of participants who complete the Cyber Essentials program gain new insights with each attempt, underscoring the value of ongoing education and development in this fast-evolving field.
The Vital Role of Law Enforcement and Government in Strengthening Cybersecurity
Adam acknowledges that law enforcement agencies and government bodies play a crucial role in assisting businesses with their cybersecurity needs. However, he also emphasizes the necessity for the industry to modernize its approach to providing support. The outdated tactics of instilling fear, uncertainty, and doubt to market cybersecurity solutions are no longer effective; businesses now require more practical, actionable guidance and support to navigate the complex landscape.
Identifying Emerging Threats and Trends in Cybercrime
The landscape of cyber threats has undergone a dramatic transformation over the past decade, with attackers consistently staying several steps ahead of organizations. A notable trend is the resurgence of social engineering attacks, exemplified by sophisticated groups such as Scattered Spider. These attacks often target IT help desks, employing advanced methods frequently supported by artificial intelligence, showcasing the evolving tactics of cybercriminals.
Adam further highlights the evolution of cybercrime dynamics from individual hackers to organized crime syndicates. These groups operate with the structure of legitimate businesses, complete with dedicated customer service teams. For example, platforms offering ransomware-as-a-service now provide legal counsel to assist in ransom negotiations, illustrating the alarming sophistication and professionalism characterizing modern cybercrime operations.
Leveraging AI’s Role in Enhancing Cybersecurity Defenses
Artificial intelligence serves as a dual-edged sword in the realm of cybersecurity. While it enhances the effectiveness of social engineering attacks, it also provides valuable opportunities for defense and fortification. Adam believes that AI will play a pivotal role in empowering businesses to create more secure environments; however, it also introduces new challenges that organizations must proactively address to stay ahead of potential threats.
Fostering a Security-Conscious Culture within Organizations for Enhanced Cybersecurity
Establishing a culture of security awareness is essential for a robust cybersecurity strategy. Adam emphasizes the importance of embedding security principles within the core of an organization’s culture, beginning with the development of clear mission and vision statements. This comprehensive approach ensures that every employee understands their vital role in maintaining security within the organization, fostering a collective commitment to cybersecurity.
To effectively engage employees, Adam advocates for making training relatable to their everyday lives. For instance, illustrating the repercussions of losing personal data, such as cherished photographs on social media platforms, can significantly enhance their understanding of the importance of cybersecurity in a practical and meaningful way. This connection not only raises awareness but also encourages proactive behavior towards security measures.
Adopting Frameworks for Cybersecurity Maturity and Continuous Growth
For organizations embarking on their cybersecurity journey, Adam strongly recommends implementing structured frameworks such as Cyber Essentials. These frameworks provide a clear, methodical approach to establishing security measures, helping businesses to avoid feelings of overwhelm while laying a resilient foundation. By following these guidelines, organizations can systematically improve their cybersecurity posture and reduce vulnerabilities.
He also highlights the critical importance of ongoing improvement, as cybersecurity is an ongoing process rather than a one-time initiative. Organizations must continuously adapt and evolve their security measures to meet the ever-changing threat landscape and dynamic environments in which they operate, ensuring that they remain resilient against emerging threats.
Envisioning the Future of Cybersecurity: Opportunities and Challenges Ahead
Adam expresses optimism regarding the growing public awareness of cybersecurity. As younger generations become more familiar with technology, they bring an enhanced understanding of cybersecurity principles into their workplaces. This shift in awareness has the potential to significantly aid businesses in cultivating stronger and more resilient security cultures that can withstand the pressures of modern cyber threats.
Furthermore, Adam identifies promising opportunities within artificial intelligence that could empower businesses to automate and fortify their security measures. However, he cautions that the rise of AI also presents new challenges that organizations must be prepared to confront, urging proactive strategies to mitigate potential risks associated with this technology.
Empowering the Next Generation through Comprehensive Cybersecurity Education
Adam emphasizes the necessity of placing greater focus on educating children about cybersecurity principles. While educational institutions currently adopt diverse approaches to teaching these concepts, a more standardized curriculum could better equip the next generation for navigating the complexities of the digital landscape. This education will be crucial in fostering a culture of security awareness from a young age.
Additionally, parents hold a significant responsibility to teach their children about online safety. Adam advocates for the establishment of clear boundaries regarding device usage and the importance of educating children about the risks associated with sharing personal information online, ensuring they are better prepared to navigate the digital world safely.
Key Takeaways from Adam Pilton’s Journey: Overcoming Cybersecurity Challenges
Adam Pilton’s remarkable journey from police officer to cybersecurity professional offers invaluable insights into the profound human impact of cyber threats and the urgent need for practical, actionable security measures. As businesses navigate the intricate realm of cybersecurity, structured frameworks like Cyber Essentials can serve as a solid foundation for developing a resilient security posture that effectively safeguards their assets.
The future of cybersecurity is filled with potential, characterized by heightened awareness and the transformative power of AI to enhance security measures. Nevertheless, this evolving landscape also introduces new challenges that businesses must actively address. By prioritizing security awareness, cultivating an inclusive culture, and committing to continuous improvement, organizations can effectively stay ahead of emerging threats and protect their most valuable assets.
The post Cybersecurity Insights: From Police to CISO appeared first on Ezi Gold.
The Article Cybersecurity Insights: Transitioning from Police to CISO Was Found On https://limitsofstrategy.com
-

Top Security Picks for Entry Level Estates in Umhlanga
Discover Affordable Entry-Level Estates in Umhlanga: Your Comprehensive Guide
Understanding the Concept of Entry-Level Estates in Umhlanga

An entry-level estate is specifically designed to provide affordable luxury for those stepping into the housing market, particularly first-time buyers or individuals searching for budget-friendly housing options. These estates are thoughtfully constructed to strike a harmonious balance between comfort and cost, cultivating a friendly atmosphere that promotes community living. Common characteristics that define these estates typically include:
- Modern architectural designs that maximize both space efficiency and functionality, catering to contemporary lifestyles.
- Proximity to essential amenities, such as parks, shops, and schools, ensuring ease and convenience for residents.
- Facilities that encourage community interaction, like clubhouses and recreational areas, which foster social connections.
- Well-maintained gardens and communal spaces that invite outdoor activities and gatherings.
By offering a diverse range of services and environments, these estates successfully cater to various lifestyles while remaining financially accessible for many individuals and families eager to find their dream home.
Key Security Features Found in Umhlanga Estates
Security is a top priority in the estates of Umhlanga, where sophisticated measures are implemented to ensure the safety and well-being of all residents. The adoption of these security features is vital in providing homeowners with peace of mind, allowing them to fully enjoy their living spaces without the constant concern for safety. Common security measures typically include:
- 24/7 surveillance through CCTV cameras monitoring high-traffic and critical areas within the estate.
- Biometric access systems that limit entry to authorized individuals, bolstering overall security.
- Regular patrols conducted by trained security personnel to maintain a visible presence and deter potential threats.
- Secure perimeter fencing, complemented by access control points, which enhances the overall safety of the community.
The combination of these security measures not only protects residents but also significantly boosts the overall value of properties within the estate, making them more attractive to potential buyers seeking safe living environments.
Enjoyable Amenities That Enhance Life in Entry-Level Estates
The amenities available in entry-level estates are crucial in elevating residents’ lifestyles, providing ample opportunities for recreation, relaxation, and social interaction. Many of these estates are intentionally designed to foster a sense of community while offering essential facilities that cater to modern living needs. Common amenities featured in these estates often include:
- Swimming pools that provide a refreshing retreat during hot weather, ideal for relaxation and social gatherings.
- Fitness centres equipped with modern exercise machines, catering to health-conscious residents.
- Communal parks and gardens designed for relaxation and family outings, encouraging outdoor enjoyment.
- Children’s play areas that are specifically created to facilitate safe and engaging outdoor activities for younger residents.
These amenities not only enrich daily living but also contribute to a vibrant community spirit, making entry-level estates an attractive choice for families and young professionals seeking a balanced and fulfilling lifestyle.
Expert Insights on the Best Entry-Level Estates with Security in Umhlanga

Critical Factors That Make an Umhlanga Estate Stand Out
Several factors contribute to the appeal of an estate in Umhlanga, with experts consistently identifying three primary elements: location, design, and community atmosphere. The most desirable estates are typically situated near essential amenities such as schools, shopping centres, and major transport routes, providing convenience and accessibility. Well-thought-out designs that enhance natural light and create functional living spaces further elevate their appeal. Additionally, a vibrant community atmosphere, enriched by regular events and shared spaces, adds significant value, as residents increasingly appreciate meaningful social connections.
Research shows that residents prioritize proximity to facilities and green spaces, which consistently rank high on their lists of preferences. An estate that combines aesthetic beauty with practical functionality will undoubtedly attract potential buyers in a competitive market.
Impact of Security Features on Property Value in Umhlanga Estates
The connection between enhanced security features and property value is significant, as improved safety measures can lead to increased demand from buyers seeking peace of mind. Properties situated within secure estates often command higher prices due to the reassurance they provide. For example, estates that feature comprehensive security systems, including gated access and continuous monitoring, have observed noticeable increases in property values over time.
Real-world examples illustrate this trend effectively. Estates such as The Pearls of Umhlanga, known for their stringent security measures, have experienced steady appreciation in property values. With buyers becoming increasingly selective about safety, they are more likely to invest in estates that prioritize security, consequently driving up overall market value in the area.
Emerging Trends Influencing the Future of Entry-Level Estates

Current trends shaping entry-level estates in Umhlanga reflect broader societal shifts towards sustainability and technology integration. Eco-friendly designs are becoming more prevalent, with developers placing a strong emphasis on energy efficiency and sustainable materials in their new constructions. Additionally, the rise of smart home technology allows homeowners to gain enhanced control over their living environments through automated systems for lighting, security, and climate management.
To remain competitive amidst these trends, developers should contemplate incorporating flexible living spaces that adapt to the evolving needs of buyers, such as multifunctional rooms that can serve as home offices or guest accommodations. By staying attuned to these advancements, they can create estates that not only attract buyers but also foster long-term satisfaction and community involvement.
Top 5 Recommended Entry-Level Estates in Umhlanga You Should Consider
Estate 1: Unique Features and Community Benefits
The first estate to highlight is Estate 1, which seamlessly blends affordability with luxurious living. Its modern designs are complemented by essential amenities that cater to both young professionals and families. Residents benefit from spacious layouts and contemporary finishes, creating a stylish living environment that aligns with modern lifestyles.
Beyond aesthetics, Estate 1 prioritizes community-oriented facilities, such as a clubhouse for hosting events and a swimming pool for relaxation during the hot summer months. The estate’s dedication to enhancing quality of life is evident, with beautifully landscaped gardens and play areas tailored specifically for children, creating an ideal setting for family living.
Another notable aspect is its prime location, which provides convenient access to shopping centres, schools, and recreational areas. With its attractive features and strategic positioning, Estate 1 stands out as a top choice for entry-level buyers exploring opportunities in Umhlanga.
Estate 2: Exceptional Location and Connectivity
Estate 2 is strategically located near key amenities and transport links, making it an ideal option for those who value convenience and connectivity. Residents are just a short drive from major shopping centres like Gateway Theatre of Shopping, which offers a wide array of retail choices and entertainment options.
Accessibility is further enhanced by its proximity to major highways, ensuring a straightforward commute to nearby business districts and the bustling Durban city centre. The estate’s location not only simplifies daily life but also supports property value retention, as homes in well-connected areas tend to appreciate more steadily over time.
Moreover, Estate 2 integrates modern safety measures, including biometric access control and continuous security patrols, ensuring that residents feel secure and protected in their homes. The combination of location, safety, and accessibility makes Estate 2 a compelling choice in the Umhlanga property market.
Estate 3: Cultivating Community Engagement and Lifestyle Amenities
Estate 3 excels at fostering a vibrant community atmosphere, offering a variety of events and shared spaces that significantly enhance the living experience for its residents. Regular community gatherings, such as weekend markets and family fun days, create opportunities for neighbours to connect, fostering a sense of belonging that is often lacking in traditional housing environments.
In addition to communal events, Estate 3 features beautifully landscaped gardens and walking trails that encourage outdoor activities and promote a healthy, active lifestyle. Amenities such as a gym and sports courts further support residents’ well-being, making it convenient for them to engage in physical activities without needing to leave the estate.
The estate’s commitment to community-oriented living is complemented by robust security measures, ensuring that residents can enjoy their surroundings without concerns for their safety. This blend of lifestyle, community engagement, and security makes Estate 3 a standout option for potential buyers seeking a genuine sense of home in Umhlanga.
Essential Tips for Selecting the Ideal Entry-Level Estate in Umhlanga
Key Factors to Evaluate When Choosing Your Estate
Selecting the perfect entry-level estate necessitates a careful assessment of several key factors that will significantly influence your living experience and long-term investment. Important elements to consider include your budget, desired amenities, security levels, and proximity to workplaces or schools. Buyers should engage in self-reflection by asking:
- What is my budget, including monthly levies and rates?
- What amenities are critical for my lifestyle and family needs?
- What level of security is necessary for my peace of mind?
- How close should I be to my workplace, schools, and public transport?
By providing comprehensive answers to these questions, prospective buyers can clarify their ideal estate, ensuring that it meets their practical needs and lifestyle aspirations.
Understanding the Importance of Estate Location in Your Decision
The estate’s location plays a crucial role in determining lifestyle choices, commute times, and property value, making it a central factor in the decision-making process. A well-located estate can significantly enhance daily living, offering quick access to essential services and recreational opportunities. Properties situated near schools, shopping centres, and healthcare facilities fulfill daily needs while contributing to a higher quality of life for residents.
Moreover, location often directly impacts property value. Estates located in desirable areas generally appreciate more rapidly, providing long-term financial benefits to homeowners. Buyers should consider both current accessibility and potential future developments in the area, as these factors can greatly influence long-term property values and lifestyle experiences.
Long-Term Benefits of Investing in Entry-Level Estates
Investing in an entry-level estate presents numerous long-term financial advantages, including potential appreciation and a pathway to more luxurious properties in the future. The initial investment serves as a stepping stone, enabling buyers to build equity over time. As property values in Umhlanga rise due to its increasing popularity, homeowners can anticipate substantial financial gains upon selling.
Additionally, the community aspect of entry-level estates fosters a supportive neighbourhood, leading to increased satisfaction and stability for families. Many residents discover that living in an entry-level estate creates opportunities for social connections and lasting friendships, ultimately enriching their overall quality of life. This combination of financial and social benefits makes investing in an entry-level estate a worthwhile consideration for prospective buyers.
Exploring Financing Options for Entry-Level Estates
A variety of financing options are accessible for those looking to purchase entry-level estates in Umhlanga, with tailored solutions designed to accommodate different financial situations. Traditional mortgages are commonly available, offering both fixed-rate and adjustable-rate options that allow buyers to select a plan that aligns with their income and financial goals.
Additionally, government schemes and incentives may assist first-time buyers, providing grants or subsidies to help with down payments and closing costs. These options can significantly alleviate the financial burden of purchasing a home. Developers may also offer financing assistance or affordable payment plans, making homeownership more attainable for potential buyers.
By exploring the diverse financing options available, buyers can identify a solution that best suits their needs, making the dream of owning property in Umhlanga a practical reality.
Comprehensive Financing Options for Entry-Level Estates in Umhlanga
Mortgage Options for Aspiring Homeowners to Consider
A variety of mortgage options are available for prospective homeowners in Umhlanga, each designed to meet different financial circumstances and preferences. Fixed-rate mortgages provide stability with consistent monthly payments, making budgeting easier for homeowners. Conversely, adjustable-rate mortgages may start with lower introductory rates, appealing to those who anticipate their income will rise over time.
Moreover, some financial institutions offer specialized loans designed specifically for first-time buyers, often featuring lower interest rates or reduced down payment requirements. Buyers should carefully assess their financial situation and future plans when selecting a mortgage type, as this choice will significantly impact their long-term financial health.
Understanding the various mortgage products available ensures that buyers can navigate the financing landscape effectively and choose the best option for their unique circumstances.
Accessing Financial Assistance for First-Time Buyers
First-time buyers may have access to various forms of financial assistance that significantly ease the process of purchasing an entry-level estate. Government subsidies and grants, such as those provided through the Finance Linked Individual Subsidy Programme (FLISP), are specifically designed to assist lower-income earners with down payments and related costs.
Furthermore, local banks and financial institutions may offer special programmes tailored for first-time buyers, providing favorable terms that enhance affordability. Engaging with a qualified real estate agent or financial adviser can also yield valuable insights into available assistance, ensuring that buyers do not miss out on beneficial opportunities.
Securing financial assistance can drastically reduce the initial barriers associated with homeownership, making it a realistic goal for many first-time buyers in Umhlanga.
Advantages of Rent-to-Own Schemes for Buyers
Rent-to-own schemes provide a practical pathway for buyers who may not yet be ready to purchase a property outright. This arrangement allows individuals to rent a home with the option to buy it after a specified period, giving them time to enhance their financial standing or save for a larger deposit.
One significant advantage is that it allows buyers to lock in the purchase price, protecting them from potential market fluctuations. Additionally, a portion of the rent paid can often contribute towards the eventual down payment, making it a feasible financial strategy for many buyers.
Rent-to-own schemes also offer buyers the chance to experience both the community and the property before making a full commitment, enabling more informed decision-making. For many, this flexibility makes the journey to homeownership more manageable and less daunting, serving as a vital stepping stone toward achieving their housing goals.
Benefits of Low-Interest Loans for Entry-Level Estates
Low-interest loans can significantly enhance affordability for those looking to purchase entry-level estates in Umhlanga. These loans lower the overall cost of borrowing, enabling buyers to pay less in interest throughout the loan’s duration. Consequently, monthly repayments become more manageable, freeing up disposable income for other essential expenses.
Moreover, lower interest rates can increase purchasing power, allowing buyers to afford more desirable properties or additional amenities. Many financial institutions provide low-interest loans specifically aimed at first-time buyers, making it crucial for prospective homeowners to explore and compare options.
By leveraging low-interest loans, buyers can alleviate their financial burdens while taking a substantial step towards securing their home in one of Umhlanga’s entry-level estates.
Shared Ownership Schemes: A Solution for First-Time Buyers in Umhlanga
Shared ownership schemes offer an innovative solution for first-time buyers who may find full property ownership financially challenging. These arrangements enable individuals to purchase a portion of a property, typically between 25% and 75%, while paying rent on the remaining share.
One primary advantage is that shared ownership significantly lowers the initial financial outlay required to enter the property market. This can be especially beneficial in areas like Umhlanga, where property prices are steadily rising. Furthermore, as homeowners gradually increase their share in the property, they can build equity over time, aiding in long-term financial planning.
Additionally, shared ownership schemes often come with reduced maintenance responsibilities, allowing buyers to enjoy homeownership without the full burden of upkeep. For many first-time buyers in Umhlanga, these schemes provide a practical route to property ownership, making it more accessible and sustainable compared to traditional methods.
Strategies for Securing the Best Entry-Level Estates with Security in Umhlanga
Effective Negotiation Techniques for Property Buyers
Negotiation is a critical element in securing the best deal when purchasing an entry-level estate. Employing effective negotiation strategies can greatly influence the affordability of your property purchase, allowing you to maximize your investment. Potential buyers should begin by conducting thorough market research to comprehend current property values, trends, and comparable sales in the area.
Armed with this information, buyers can approach negotiations confidently, prepared to discuss price adjustments based on comparable properties or necessary repairs. Additionally, expressing genuine interest and flexibility regarding closing dates can enhance your bargaining position, as sellers often prefer negotiating with committed buyers who demonstrate serious intent.
Engaging a skilled real estate agent may also prove advantageous, as they can leverage their expertise and industry connections to negotiate effectively on your behalf. By employing these strategies, buyers can secure a deal that not only fits their budget but also ensures satisfaction with their new home.
Timing Your Property Purchase: Best Times to Buy in Umhlanga
Timing the property market can significantly enhance the potential for securing advantageous deals in Umhlanga. Typically, the optimal times to buy align with periods of lower demand, such as the winter months or during the festive season when fewer buyers are actively searching for properties.
During these periods, sellers may be more inclined to negotiate on price or terms, creating opportunities for savvy buyers to secure exceptional deals. Furthermore, keeping informed about local market trends and economic factors can aid in identifying the ideal time to buy. For instance, if signs of an economic downturn or shifts in employment rates emerge, it may be wise to enter the market before potential price reductions occur.
By monitoring market conditions and timing strategically, buyers can maximize their chances of finding the right entry-level estate at a competitive price.
Conducting Thorough Due Diligence on Your Potential Estate
Conducting comprehensive due diligence is an essential step in the home-buying process, especially when considering an entry-level estate. This process involves investigating various aspects of the property and the estate to ensure that it meets your requirements and to uncover any potential issues.
Key areas to focus on during due diligence include reviewing legal documents such as the title deed and homeowner association rules, inspecting the property for maintenance concerns or defects, and assessing the estate’s financial health by reviewing budgets and reserve funds.
Engaging professionals, such as property inspectors and legal advisers, can provide valuable insights and help identify any red flags that may impact your decision. By ensuring comprehensive due diligence, buyers can make informed choices and avoid costly mistakes in their pursuit of a new home.
Assessing Security Features When Choosing an Estate
When selecting an entry-level estate, understanding the security measures in place is crucial for ensuring a safe living environment. Essential security features to consider include CCTV surveillance, which can deter criminal activity and provide a record of incidents if necessary. Additionally, gated access systems that restrict entry to authorized individuals enhance the overall safety of the estate.
Regular patrols by trained security personnel represent another vital component, as a visible security presence can greatly increase residents’ peace of mind. It is also beneficial to inquire about the estate’s community policies on security, as transparent communication regarding safety measures can reflect the estate’s commitment to resident well-being.
By meticulously evaluating the security features of an estate, potential buyers can make informed decisions that align with their safety priorities and lifestyle preferences, ensuring the security of their future home.
Evaluating the Long-Term Value of an Estate
Assessing the long-term value of an estate is a critical consideration for buyers, especially in a dynamic property market like Umhlanga. Factors influencing potential appreciation include location, availability of amenities, and community development plans. Properties located in desirable areas with easy access to schools, transport, and recreational facilities tend to experience steadier appreciation over time.
Additionally, examining the quality of construction and the reputation of the developer can provide valuable insights into the durability and potential value of the estate. Buyers should also consider community growth prospects, including future developments or infrastructure projects that may enhance the area’s appeal and desirability.
By conducting a thorough assessment of these factors, buyers can make informed decisions about their investments, ensuring that they select an entry-level estate with strong potential for long-term value growth.
Lifestyle and Community Dynamics in Umhlanga’s Entry-Level Estates
Engaging Activities Available to Residents
Residents of Umhlanga’s entry-level estates can engage in a variety of activities that cater to diverse interests and lifestyles. Many estates feature communal facilities such as sports courts, swimming pools, and fitness centres, promoting an active lifestyle and encouraging residents to engage in physical activities.
In addition to sports and fitness, social events play a significant role in fostering community spirit. Regularly organized activities, such as movie nights, family picnics, and seasonal festivals, provide opportunities for neighbours to connect and build lasting relationships. Many estates also feature shared gardens or parks, where residents can gather for leisurely strolls or children’s playdates, facilitating social interactions.
By offering a rich array of activities that promote both physical health and social interaction, entry-level estates in Umhlanga contribute to a fulfilling lifestyle for their residents, enhancing their overall living experience.
Cultivating a Sense of Belonging Within the Community
A strong sense of community is integral to life in Umhlanga’s entry-level estates, nurtured through various initiatives designed to promote connection and engagement among residents. Regular events, such as community clean-up days and seasonal celebrations, encourage participation and collaboration, allowing residents to contribute to their neighbourhood while forging relationships.
Shared spaces, including clubhouses and gardens, serve as focal points for interaction, creating opportunities for informal gatherings and organized activities. Additionally, many estates have established communication channels, such as newsletters or social media groups, to keep residents informed about upcoming events and community news, enhancing overall community engagement.
This focus on community involvement not only cultivates a sense of belonging but also elevates the overall quality of life for residents, making entry-level estates in Umhlanga attractive choices for individuals and families seeking connection and support within their neighbourhood.
Benefits of Living in a Gated Community
Residing in a gated community offers numerous advantages that contribute to an enhanced quality of life for residents. One of the most notable benefits is the increased security provided by controlled access, which deters unauthorized individuals from entering the estate. This heightened sense of safety allows residents to feel more comfortable in their homes and the surrounding environment.
Gated communities typically feature well-maintained communal spaces and amenities, such as parks, swimming pools, and recreational facilities, promoting an active and social lifestyle. Furthermore, the presence of neighbours within a gated community fosters a sense of camaraderie, as residents often share common interests and engage in social activities together, enriching the community experience.
The combination of security, shared amenities, and a close-knit community makes living in a gated estate an appealing choice for many families and individuals seeking to enhance their living experience in Umhlanga.
Common Amenities Found in Entry-Level Estates
Amenities in entry-level estates significantly enrich the living experience, providing residents with convenient access to essential services and recreational opportunities. Many estates include features such as swimming pools, fitness centres, and communal gardens, which cater to diverse interests and promote a healthy lifestyle for residents of all ages.
Additionally, some estates offer children’s play areas, ensuring that families can provide safe and engaging spaces for their children to play and socialize with neighbours. Clubhouses often serve as focal points for community events, providing a venue for residents to gather, organize social activities, and foster connections with one another.
By offering a wide range of amenities, entry-level estates effectively transform living environments into vibrant communities, significantly enhancing the convenience and enjoyment of everyday life for residents.
Influence of Location on Residents’ Lifestyle Choices
The strategic location of Umhlanga’s entry-level estates plays a vital role in shaping residents’ lifestyle choices and leisure activities. Proximity to stunning beaches, shopping centres, and dining options provides residents with a wealth of opportunities for recreational activities, social engagements, and convenient access to essential services.
Residents can easily partake in outdoor activities such as beach outings, water sports, and hiking, contributing to an active and fulfilling lifestyle. Furthermore, the presence of quality schools and healthcare facilities nearby simplifies the process for families to balance work and personal commitments, enhancing overall daily living.
Ultimately, the location of these estates significantly influences lifestyle choices, allowing residents to enjoy a vibrant and well-rounded life while remaining connected to all the amenities they value and require.
Future Developments and Trends in Umhlanga’s Entry-Level Estates
Upcoming Projects Shaping the Future of Umhlanga
Umhlanga’s property market is continually evolving, with several new entry-level estate projects in the pipeline aimed at meeting the growing demand for affordable housing solutions. These developments are anticipated to introduce modern designs and innovative amenities, catering to the needs of contemporary buyers seeking quality homes.
Planned projects typically focus on integrating sustainable design principles, including energy-efficient features and eco-friendly materials. This aligns with the increasing demand for green living solutions, ensuring that new estates appeal to environmentally conscious buyers looking for sustainable lifestyles.
Moreover, many new developments aim to enhance community engagement through the creation of shared spaces, parks, and recreational facilities. As these projects come to fruition, Umhlanga’s entry-level estates will continue to evolve, providing residents with improved living environments and access to modern conveniences that meet their needs and aspirations.
Transformative Impact of Technology on Future Estates
Advancements in technology are poised to significantly influence both the design and functionality of future entry-level estates in Umhlanga. Smart home technology is becoming increasingly prevalent, allowing homeowners to control various aspects of their living environment, such as lighting, security systems, and climate control, all through mobile devices.
Developers are also exploring the integration of energy-efficient systems, such as solar panels and smart thermostats, aimed at reducing utility costs and minimizing environmental impact. These innovations not only enhance the appeal of new estates but also align with the growing demand for sustainable living solutions, making them more attractive to prospective buyers.
By embracing technological advancements, future entry-level estates will offer residents enhanced convenience, comfort, and efficiency, fundamentally transforming the way they experience homeownership and daily living.
Predictions for Property Value Growth in Umhlanga
Expert predictions indicate a positive outlook for property value growth in Umhlanga, driven by the area’s increasing popularity and ongoing development initiatives. As more buyers seek entry-level homes within a vibrant community, demand is expected to rise, contributing to steady appreciation in property values over the coming years.
Moreover, the ongoing investment in infrastructure and amenities is likely to further enhance the area’s appeal, attracting new residents and increasing competition for available properties. Consequently, buyers investing in entry-level estates in Umhlanga can anticipate favorable long-term value retention and potential appreciation, solidifying Umhlanga’s status as a desirable property market.
With a focus on future developments and emerging trends, Umhlanga remains a promising investment destination for those seeking entry-level estates characterized by security and a strong community foundation.
Frequently Asked Questions about Entry-Level Estates in Umhlanga
What is the average cost of entry-level estates in Umhlanga?
The average price can vary significantly based on location and amenities but typically ranges from R1.5 million to R3 million.
Are there specific financing options for first-time buyers in Umhlanga?
Yes, various financing options exist for first-time buyers, including government grants and specialized mortgage products tailored to their needs.
What amenities should I consider when evaluating an entry-level estate?
Key amenities to consider include swimming pools, fitness centres, parks, and communal areas designed for socializing and community engagement.
How important is security in the selection of an estate?
Security is crucial, as it greatly impacts residents’ peace of mind and can enhance property values over time.
What is the typical size of homes in entry-level estates?
Homes generally range from 80 to 150 square metres, depending on the estate and design specifications.
How does location influence property values in Umhlanga?
Location significantly affects property values, with estates near schools and amenities tending to appreciate more quickly due to demand.
Are community events organized in entry-level estates?
Yes, many estates host regular community events that cultivate neighbourly connections and enhance social engagement among residents.
What should I focus on when inspecting a property?
During an inspection, concentrate on the condition of the property, security features, and compliance with local regulations to ensure a sound investment.
Can I invest in property with a low income?
Yes, various programs and schemes are designed to assist low-income buyers in entering the property market and securing financing.
What are the steps involved in purchasing a property in Umhlanga?
The process typically involves securing financing, conducting due diligence, negotiating the price, and finalizing the purchase contract with the seller.
Explore our world on YouTube – subscribe now!
The Article Best Entry Level Estates With Security In Umhlanga: Top Picks First Published On: https://revolvestate.com
The Article Entry Level Estates in Umhlanga: Top Security Picks Was Found On https://limitsofstrategy.com
-

Prepper Home Security: Key Tips and Strategies for Safety
Elevate Your Home Security with Robust Physical Barriers and Strategic Fortifications
Strengthen Your Property’s Defense with Durable Fencing and Resilient Gates

To enhance your prepper home security, it is imperative to establish a fortified perimeter. This serves as a crucial deterrent against unauthorized intruders. Begin by selecting robust materials such as steel or pressure-treated wood for your fencing and gates, as these materials offer superior strength and longevity. Opt for designs that enable clear visibility of your surroundings, thus allowing for the early detection of any suspicious activities. Furthermore, ensure that your gates are equally fortified and equipped with tamper-resistant locking mechanisms, which add an extra layer of security. Homeowners from various environments, including suburban neighborhoods in the United States and rural properties in Australia, can significantly bolster their security by installing such physical barriers, providing both protection and peace of mind.
Installing fencing should be viewed as more than just an aesthetic enhancement; it is a fundamental aspect of your security strategy. Ensure that the fence is anchored deep into the ground to thwart attempts by intruders to dig beneath it. Height is also a critical factor; ideally, fences should reach a minimum height of six feet to deter easy climbing. Consider incorporating decorative spikes or pointed tops to further discourage would-be trespassers, creating a psychological barrier that deters unlawful entry. Additionally, integrating natural elements like thorny bushes along the fence line not only increases security but also beautifies your landscape, making it more inviting yet secure.
The effectiveness of your security measures is contingent not only on the physical barriers you establish but also on their strategic placement around your property. Conduct a thorough assessment to identify vulnerable spots—these may include hidden corners or areas that necessitate taller or reinforced fencing. Consulting with local security professionals can provide customized insights tailored to your specific region and climate, ensuring that your fencing approach is not only effective but also compliant with local regulations and standards.
Enhance Your Safety with Reinforced Doors and Shatter-Resistant Windows
Doors and windows represent some of the most vulnerable entry points in any home, underscoring the importance of investing in reinforced materials for these critical areas as part of a comprehensive prepper home security plan. Choose steel doors or solid wood doors, each equipped with additional deadbolts, as these features drastically reduce the likelihood of forced entry. Regardless of whether you reside in a bustling urban area or a peaceful rural setting, prioritizing the strength of your doors should be a fundamental element of your overall security strategy.
Windows also require special attention to detail. Utilizing laminated or tempered glass significantly increases the difficulty for intruders attempting to break in, compared to standard glass. Consider installing locks that necessitate keys for added security. Many security professionals recommend applying window film, which helps hold shattered glass fragments together, making break-ins more difficult and buying homeowners valuable time to react during emergencies.
The installation method is equally significant when it comes to fortifying these access points. Ensure that door frames are sturdy and properly secured to the walls to provide resistance against forced entry attempts. For windows, consider installing security screens or grilles that blend functionality with aesthetic appeal, providing peace of mind without compromising the exterior charm of your home.
Moreover, enhancing these access points with alarm systems that trigger when unauthorized openings occur can serve as a vital line of defense. These systems not only alert homeowners to intrusions but can also notify local authorities, guaranteeing a swift response in emergencies.
Create Designated Safe Rooms and Panic Areas for Emergency Situations
Establishing safe rooms or panic areas is a critical component of prepper home security. These specific spaces provide a secure haven during crises, including home invasions or natural disasters. Ideally, a safe room should be positioned away from vulnerable entry points like doors and windows, creating a defensive area where residents can remain protected until help arrives.
When planning your safe room, consider reinforcing the walls and doors to withstand potential threats. Stock the room with essential supplies such as water, non-perishable food, first aid kits, and communication devices to maintain contact with emergency services. Having a backup power source, such as a battery-powered generator, will ensure the room remains functional even during power outages, significantly boosting your preparedness.
Globally, families are increasingly prioritizing the creation of safe rooms, recognizing the importance of being ready for emergencies. In urban settings, existing closets or basements can serve effectively as panic areas, while rural homes may dedicate a portion of their basement or construct an additional structure in the yard for enhanced security and peace of mind.
Equipping these safe areas with communication devices, like dedicated landlines or walkie-talkies, enables continuous contact with the outside world, enhancing your overall sense of security. Furthermore, developing a family plan that includes the safe room’s location and protocols for accessing it during emergencies can ensure that all family members know how to respond swiftly and effectively.
Boost Security Deterrence with Strategic Lighting and Surveillance Solutions

Crime deterrence relies heavily on visibility, making security lighting and surveillance an essential part of a robust prepper home security strategy. Utilizing motion-sensor lights can illuminate dark areas surrounding your property, thereby minimizing the chance of intruders finding hiding spots. Position these lights near entry points and along pathways to enhance safety, particularly in neighborhoods that may lack adequate lighting at night.
Incorporating surveillance cameras can greatly improve your home security. Strategically place cameras to monitor all entry points and vulnerable areas like garages and backyards, creating a comprehensive surveillance system. Ensure these cameras come equipped with night vision capabilities to capture clear footage even in low-light conditions. Homeowners worldwide, from bustling urban centers to quiet suburbs, have found that the mere visibility of cameras can effectively deter criminal activity.
Regular maintenance of both lighting and camera systems is crucial to ensure they perform optimally when needed. Schedule routine checks on batteries and wiring for motion sensors and cameras to guarantee constant functionality. Many modern systems are now compatible with smartphone applications, allowing homeowners to monitor their properties remotely and receive immediate alerts when motion is detected.
Integrating your lighting and surveillance systems into a smart home setup offers improved control and convenience. Smart home applications empower you to schedule lighting or receive instant notifications, creating the illusion that your property is occupied even when you are away, thus further enhancing security.
Adopt Comprehensive Surveillance and Monitoring Solutions
Enhance Your Security with Strategically Placed CCTV Cameras
CCTV cameras play a foundational role in modern home security systems for preppers. However, the success of these systems hinges on their strategic placement around your property. It is essential to cover all entry points, including front and back doors, garages, and any windows that may serve as easy targets for intruders. Furthermore, consider positioning cameras in less visible yet vulnerable areas, such as side entrances or pathways leading toward the home.
When selecting cameras, choose high-definition models capable of capturing clear images both day and night. Many homeowners favor cameras that feature two-way audio, allowing communication with anyone near the camera, whether it be a delivery person or a potential intruder. The capability to monitor real-time video feeds from anywhere in the world significantly enhances peace of mind for homeowners, enabling them to keep an eye on their properties remotely.
Additionally, consider how your camera system integrates with other security measures. For example, connecting your CCTV system with alarm notifications can create dual layers of security. Any detected movement can trigger alerts, enabling immediate action, whether that means notifying authorities or monitoring the situation yourself.
It’s vital to communicate the presence of CCTV cameras through visible signage. This not only acts as a deterrent but also signals that your home is under surveillance, discouraging potential intruders who prefer softer targets.
Fortify Security with Motion Sensors and Alarm Systems

Motion sensors and alarms significantly elevate prepper home security by providing immediate notifications in case of unauthorized movement. These systems can be installed both indoors and outdoors, creating a comprehensive network that detects activity in critical areas. Outdoor motion sensors can trigger both lights and alarms, making it much more challenging for intruders to approach unnoticed.
When implementing motion sensor technology, consider adjusting sensitivity settings to meet your specific requirements. These systems can differentiate between human movement and that of smaller animals, thereby minimizing false alarms. A well-calibrated system enhances your security without causing unnecessary disturbances within your household.
Indoor motion sensors are particularly valuable in areas of high traffic within the home. When combined with an alarm system, they can provide alerts not only to homeowners but also to local law enforcement. This rapid response capability can be vital, especially in regions with high crime rates, where every second counts.
Regular testing of motion sensors and alarms is essential to ensure they function correctly. Homeowners should establish a routine schedule to verify that all systems are operational, which includes checking battery life and connectivity to alarm systems.
Integrating your alarm system with a mobile application enables real-time monitoring and alerts. This level of transparency empowers homeowners to stay informed about their security even when they are away from home, maintaining a sense of control over their property.
Stay Informed with Remote Monitoring and Instant Alerts
In our fast-paced world, effective prepper home security includes remote monitoring systems that offer real-time alerts and updates. Homeowners can significantly benefit from surveillance technologies that allow monitoring via smartphones or computers, providing peace of mind and enabling them to keep an eye on their property from anywhere in the world.
These systems often utilize cloud-based storage solutions, offering secure access to video footage and alerts sent directly to your devices. Some advanced systems also incorporate facial recognition technology, allowing homeowners to quickly identify visitors or potential threats.
Moreover, remote monitoring systems can seamlessly integrate with smart home technology. For instance, smart locks can empower homeowners to remotely lock or unlock doors, ensuring that trusted individuals can access their homes even when they are not present. This not only enhances security but also increases convenience, particularly for families with multiple caregivers or service providers.
Furthermore, alerts can be customized according to your preferences. For example, you can set notifications for specific times or activities, such as when your children return home from school. This level of control can significantly enhance your household’s safety and management.
As smart home technology becomes increasingly prevalent, investing in secure systems that protect your data from potential cyber threats is essential. Always opt for reputable brands and ensure that your systems are regularly updated to defend against vulnerabilities.
Enhance Your Security with Advanced Access Control Systems
Implementing access control systems is vital for strengthening the security of a prepper’s home. These systems manage entry and exit points, ensuring that only authorized individuals gain access to your property. Keyless entry systems, which utilize keypads or smartphone applications, have grown in popularity due to their convenience and enhanced security features.
These systems eliminate the need for physical keys, which can be easily lost or stolen, allowing for straightforward management of who can enter your home. Homeowners can grant temporary access to family members, service providers, or guests without compromising overall security. The ability to change access codes regularly adds an extra layer of protection and flexibility.
Biometric locks represent another innovative solution in access control, utilizing fingerprint or facial recognition technology to permit entry. These systems are particularly effective in homes with multiple residents, ensuring that only authorized individuals can enter specific areas. Biometric locks are gaining popularity worldwide, catering to the growing demand for enhanced home security.
Moreover, integrating access control systems with surveillance cameras provides an additional layer of security. For instance, if unauthorized entry is detected, the system can alert homeowners while simultaneously recording the event. This integration creates a comprehensive security approach adaptable to various scenarios.
As smart home technology continues to evolve, exploring advanced features within access control systems will enable users to gain greater control and flexibility. Implementing such measures can significantly enhance security and provide peace of mind, especially for those residing in high-risk areas.
Maximize Security with Video Analytics and Recognition Technologies
Incorporating video analytics and facial recognition technology can elevate your prepper home security measures to unparalleled levels of efficiency and effectiveness. These systems analyze video feeds in real-time, identifying patterns and detecting unusual behaviors. This advanced technology can alert homeowners to potential threats before they escalate, helping to prevent break-ins or vandalism.
Facial recognition software enhances security by enabling homeowners to automatically identify visitors. If the system recognizes a face that is not on the approved list, it triggers an alert, allowing for immediate action. This feature is especially beneficial for families and individuals who frequently receive guests or service personnel, streamlining monitoring while enhancing safety.
Moreover, video analytics can significantly reduce false alarms. By distinguishing between human movements and inanimate objects, these systems focus on genuine threats, allowing homeowners to react appropriately without unnecessary stress. This capability not only improves response times but also maintains trust in your security system.
The implementation of these advanced technologies is becoming increasingly common globally, providing users with enhanced control over their home security. While these systems may entail higher initial costs, the investment pays dividends through increased safety and peace of mind.
Training and proper usage of these systems are crucial. Homeowners should familiarize themselves with the features and functionalities to maximize the benefits, ensuring that their prepper home security strategy is as robust as possible.
Implement Effective Access Control and Security Measures
Revolutionize Your Home Security with Keyless Entry Systems
Transforming home security, keyless entry systems represent a significant advancement for home security for preppers. These systems eliminate the need for traditional keys, dramatically reducing the risks of lockouts and unauthorized access. With the ability to use keypads or smartphone applications, homeowners can easily grant or revoke access to individuals, ensuring convenience for families and service providers alike.
Installation of keyless entry systems can be approached in various ways, from smart locks that connect to home Wi-Fi networks to standalone systems operating independently. Many homeowners appreciate the convenience of remotely managing access—granting entry to friends, family, or service personnel without needing to be physically present. This level of control allows for seamless management, particularly in busy households.
The security features integrated within these systems are also noteworthy. Numerous keyless entry systems are equipped with features such as temporary access codes, which can be easily shared with trusted individuals. These codes can be programmed to expire after a set period, further enhancing home security and providing peace of mind.
Additionally, users should remain vigilant about data security, especially when connecting smart locks to Wi-Fi networks. It’s essential to choose reputable brands that prioritize cybersecurity and offer regular updates to protect against hacking attempts. A strong password and multi-factor authentication can further enhance security.
Globally, keyless entry systems are increasingly perceived as a smart investment for homeowners looking to enhance their security measures while enjoying modern technological conveniences. As homeowners worldwide embrace these systems, the need for additional layers of security becomes paramount.
Enhance Your Protection with Biometric Locks and Secure Safes
The rise of biometric locks and safes represents a significant evolution in prepper home security, offering unparalleled levels of access control. By utilizing unique physical traits such as fingerprints or retinal scans, these systems ensure that only authorized individuals can unlock doors or safes, making them an excellent choice for securing valuables.
Biometric locks prove especially advantageous in households with multiple residents. Unlike traditional keys, which can be lost or duplicated, biometric systems offer a level of security that is difficult to replicate. Homeowners can program multiple fingerprints into the lock, allowing family members easy access while keeping unauthorized individuals at bay. This technology is gaining traction across various regions, from urban centers in North America to suburban communities in Europe.
When it comes to securing valuable items, biometric safes provide similar benefits. These safes not only deter theft but also offer an added layer of protection against accidental access by children or unauthorized guests. Many modern biometric safes are designed to be fireproof and waterproof, ensuring that crucial documents and valuables are secure from both theft and environmental hazards.
However, while biometric technology offers numerous advantages, homeowners must remain aware of potential vulnerabilities. Regularly updating the software of these systems and ensuring they are battery-operated or have a reliable backup power source can help mitigate these risks and enhance overall security.
Overall, the integration of biometric technology into home security systems reflects a growing trend in secure living, appealing to those seeking advanced solutions for their prepper home security needs.
Implement Visitor Screening and Verification for Increased Safety
Establishing protocols for visitor screening and verification is a crucial aspect of prepper home security. These measures can prevent unauthorized entry, ensuring that only trusted individuals gain access to your home, thereby creating a safer environment for all residents.
Incorporating visitor management systems can streamline the verification process. Such systems often include applications that allow residents to monitor who is at their door, enabling them to communicate with guests remotely. This feature enhances security by allowing homeowners to assess whether to grant access before physically opening the door.
Another effective strategy involves creating a secure entry protocol. This may include asking for identification from visitors or requiring appointments to be made in advance. For neighborhoods where deliveries are common, informing delivery personnel of specific entry procedures can enhance security while ensuring convenience.
Moreover, educating all household members about visitor protocols reinforces security measures and ensures a consistent approach to visitor management. Children, in particular, should be trained to recognize and respond appropriately to unknown visitors, fostering a culture of awareness and caution.
As technology advances, many homeowners are adopting smart doorbell systems equipped with cameras and two-way audio capabilities. These devices allow for real-time communication and visual verification, ensuring that residents can confirm the identity of their visitors from anywhere, making them invaluable in any prepper home security strategy.
Prepare for Emergencies with Strategic Planning
Develop Comprehensive Emergency Communication Strategies
Creating robust emergency communication plans is essential for effective prepper home security. These plans ensure that family members can coordinate their actions during a crisis, fostering a sense of safety and clarity when every second counts.
Establishing a communication hierarchy is fundamental. Designate a primary point of contact for family members to reach out to during emergencies, whether that’s a family member or a close friend living nearby. This structure streamlines communication and reduces confusion during stressful situations.
Regularly practicing emergency protocols is critical. Conduct drills to familiarize all family members with the plans, ensuring they know how to reach their designated contacts and what steps to take during various emergencies. Whether it’s a natural disaster, a home invasion, or a medical emergency, familiarity with the plan can significantly reduce panic and improve response times.
In today’s digital age, utilizing technology for communication can enhance preparedness. Many families are now using group messaging apps that allow instant communication and updates among all members. Additionally, it’s essential to have alternate communication methods in case traditional networks fail, such as walkie-talkies or satellite phones.
Building relationships within your community can also aid in emergency response. Establishing neighborhood networks can enhance support systems during crises, providing additional resources and communication channels.
Being proactive in your approach to emergency planning can make a significant difference in your family’s safety and readiness. By regularly reviewing and updating your communication plans, you can ensure that your household is well-prepared for any situation that may arise.
Identify and Practice Evacuation Routes and Drills
Identifying and consistently practicing evacuation routes is a crucial aspect of prepper home security. Homeowners should assess their properties and establish clear escape paths leading to designated safe locations. These routes should be prepared for various scenarios, including fires, natural disasters, or home intrusions.
Regular drills are essential to ensure that everyone in the household knows how to evacuate swiftly and safely. Conducting these practices not only familiarizes family members with the routes but also highlights any potential obstacles that could impede a safe exit.
When planning evacuation routes, consider multiple exits from each room, especially in high-risk areas of the home. Establish safe meeting points outside where family members can regroup after evacuating. This preparation is vital for homes with children, elderly residents, or individuals with mobility challenges.
Incorporating technology can further enhance evacuation planning. Many families now utilize mobile applications that provide maps, emergency contacts, and alerts for nearby emergencies. These resources are invaluable for families who may be traveling or away from home, ensuring that everyone has access to crucial information.
Ultimately, preparation is crucial to the success of evacuation plans. Regularly revisit and update these routes to reflect any changes in your home or community, ensuring that your family remains ready for any emergency.
Maintain Comprehensive First Aid and Medical Supplies
Maintaining a well-stocked first aid kit and medical supplies is an essential component of prepper home security. During emergencies, having immediate access to medical supplies can prevent minor injuries from escalating into serious health issues, thus ensuring the well-being of all household members.
Begin by assessing the specific needs of your household members. Include essential items such as bandages, antiseptics, gauze, and over-the-counter medications for common ailments. For families with children or pets, tailoring your first aid kit to address their specific needs is crucial for effective medical response.
Regularly check and replenish your first aid supplies to ensure everything is up to date. Many items have expiration dates, and consistently rotating your stock will ensure that you are always prepared for emergencies, thereby enhancing your household’s safety.
Additionally, consider investing in specialized training for household members. First aid and CPR courses can empower family members to act confidently during emergencies, providing crucial assistance until professional help arrives. Many communities offer these courses, making them accessible to everyone.
Incorporating a first aid plan into your emergency communication strategy can further enhance your security measures, ensuring that everyone knows who is responsible for managing medical emergencies and how to access the first aid kit.
Ultimately, a proactive approach to medical preparedness is vital in enhancing your home’s overall security and resilience in the face of unexpected situations.
Conduct Regular Emergency Training and Education
Regular training sessions and educational programs can significantly bolster prepper home security efforts. Knowledge and preparedness empower families to respond effectively during emergencies, ensuring safety and reducing panic.
These training sessions should cover a variety of critical topics, including basic first aid and CPR, as well as specific training on handling emergencies such as fires or natural disasters. Collaborating with local emergency services to facilitate workshops can provide valuable insights and resources for your community.
Engaging all family members in these educational sessions ensures that everyone is equipped with the knowledge to act confidently in emergencies. Involving children in age-appropriate training encourages responsibility and situational awareness, fostering a security-minded household.
Beyond family training, consider extending your education to your wider community. Organizing neighborhood workshops can enhance collective preparedness and build a support network among neighbors. These programs can focus on emergency response, communication strategies, and even basic self-defense techniques.
Regularly reviewing and updating your training programs based on local risks or recent emergency events can ensure that your knowledge remains current and applicable. This commitment to continuous learning significantly enhances your community’s resilience against crises.
The benefits of ongoing emergency training and education cannot be overstated. By fostering a culture of preparedness, you create a secure environment for your family and community, one that is ready to face whatever challenges arise.
Establish a Dedicated Crisis Management Team
Forming a dedicated crisis management team can elevate your prepper home security strategy. This team should comprise responsible family members or trusted friends who can take charge during emergencies, ensuring that everyone is aware of their roles and responsibilities.
The team’s primary focus should be on coordinating preparedness efforts, from developing communication plans to organizing training sessions. By assigning specific roles, such as a point of contact for external communication or a safety coordinator responsible for managing evacuation protocols, you create a clear structure for response during emergencies.
Regular meetings of the crisis management team are essential for reviewing protocols, assessing potential risks, and refining plans based on changing circumstances. This proactive approach can help identify vulnerabilities in your home security and enhance overall preparedness.
Additionally, involving local resources, such as emergency services or community leaders, can provide further insight into effective crisis management strategies. Establishing relationships with these entities ensures that your team remains informed about regional risks and available support systems.
The effectiveness of your crisis management team hinges on its ability to adapt and respond to various scenarios. Through regular training and collaboration, you can cultivate a strong sense of preparedness within your household, ensuring you are ready for any situation that may arise.
Enhance Your Perimeter Defense and Deterrence Strategies
Utilize Strategic Landscaping Techniques for Enhanced Security
Utilizing landscaping techniques for home security is an often-overlooked yet effective strategy for enhancing prepper home security. Thoughtful landscaping can bolster your property’s defenses while simultaneously creating an appealing environment that deters potential intruders.
Start by assessing the visibility of your property. Maintaining clear sightlines is crucial, as overgrown shrubs and trees can create hiding spots for potential intruders. Trim vegetation around windows and near entry points to enhance visibility for homeowners and their neighbors alike, fostering a safer community.
Incorporating thorny bushes or dense shrubs along the perimeter can deter intruders from attempting to breach your property. For instance, planting rose bushes or holly can create a natural barrier that is not only beautiful but also functional in terms of security.
Lighting plays a vital role in landscaping for security. Integrating outdoor lighting around your property, particularly along walkways and entrances, not only improves aesthetics but also enhances safety and visibility at night. Motion-sensor lights can illuminate dark corners, further discouraging unauthorized access and creating a welcoming environment.
Additionally, consider using natural barriers such as decorative fences or stone walls that provide both security and aesthetic appeal. These structures can enhance the perceived value of your property while deterring potential threats and fostering a sense of community vigilance.
Overall, thoughtful landscaping serves as both a protective measure and an enhancement to your home’s curb appeal. By integrating security features within your outdoor design, you create a welcoming yet secure environment that promotes safety.
Implement Effective Lighting and Illumination Strategies
Proper lighting is a key component of an effective prepper home security strategy. It serves as a deterrent against intruders and enhances safety for both residents and visitors. When executed correctly, lighting can create a well-illuminated environment that reduces hiding spots and increases visibility at night, promoting a secure atmosphere.
Consider implementing motion-sensor lighting that activates when movement is detected. These lights can be strategically placed near entry points, driveways, and dark corners of your yard to illuminate potentially vulnerable areas. The sudden onset of light can deter would-be intruders and alert homeowners to any suspicious activity.
In addition to motion sensors, incorporating smart lighting systems allows homeowners to control their outdoor lighting remotely. This technology can enhance security by enabling users to turn lights on or off from a distance, creating the illusion that someone is home—even when they are away, further deterring potential threats.
Another effective approach is to use pathway lighting to guide visitors safely to your front door while simultaneously illuminating the area around your home. This not only enhances aesthetics but also improves security, creating a welcoming atmosphere that conveys a commitment to safety.
Regular maintenance of outdoor lighting systems is crucial to ensure their effectiveness. It is essential to routinely check bulbs, clean fixtures, and replace any damaged components. An effective lighting system not only heightens security but also provides peace of mind for homeowners, contributing to a safe living environment.
Ultimately, the combination of strategically placed lighting and smart technology creates a formidable layer of protection for your home, enhancing your overall preparedness and promoting community safety.
Utilize Warning Signs and Decoys to Deter Intruders
In the realm of home security, perception plays a crucial role. Utilizing warning signs and decoys can significantly enhance prepper home security by creating the illusion of a well-protected property, deterring potential intruders before they even approach.
Strategically placed signs indicating that a security system is in place can deter potential intruders. These signs communicate to would-be criminals that your home is monitored, increasing the risk of being caught. Such a simple measure can drastically reduce the likelihood of a break-in, reinforcing the importance of visible security.
Incorporating decoy items, such as fake cameras or security lights, can further enhance the perception of security. While they may not provide the same level of protection as real systems, they can still create doubt in the minds of potential intruders, making them think twice before attempting to breach your property.
Additionally, consider using signage that emphasizes community watch programs or neighborhood security initiatives. This not only enhances your home’s security but also fosters a sense of community vigilance, encouraging neighbors to look out for one another.
While these measures may not comprise the core of a comprehensive security system, they serve as effective deterrents. The psychological impact of perceived security can be just as important as the physical barriers you have in place.
By integrating warning signs and decoys into your overall security strategy, you create an environment that signals preparedness and vigilance, effectively dissuading potential threats from targeting your home.
Strengthen Community and Neighborhood Security Initiatives
Join or Establish Neighborhood Watch Programs for Enhanced Security
Participating in or establishing neighborhood watch programs can significantly enhance prepper home security efforts. These community initiatives foster cooperation and vigilance, creating a united front against potential threats and enhancing safety for all residents.
Neighborhood watch programs encourage residents to take an active role in their security. Members are trained to observe and report suspicious activities, creating an environment of mutual support. The act of neighbors looking out for each other not only enhances safety but also fosters relationships within the community, building trust and camaraderie.
Effective communication is a cornerstone of these programs. Utilizing social media platforms or neighborhood apps allows residents to share information easily, from reporting suspicious activities to organizing community events. These communication channels keep residents informed and involved in local security matters, promoting a sense of responsibility.
Regular meetings and training sessions can enhance the effectiveness and preparedness of neighborhood watch programs. These gatherings offer residents the opportunity to discuss concerns, share tips, and develop strategies to improve community safety. Collaborating with local law enforcement can also provide valuable insights and resources for residents, strengthening community ties.
In areas with high crime rates, the presence of a neighborhood watch can significantly reduce incidents. By creating a collective sense of responsibility and vigilance, these programs empower communities to take charge of their safety and security.
Ultimately, establishing or joining a neighborhood watch program can create a safer living environment, reinforcing the importance of community in enhancing prepper home security and fostering a supportive network.
Develop Communication Networks and Alert Systems for Community Safety
Setting up communication networks and alert systems within your community is crucial for enhancing prepper home security. These systems enable residents to quickly share information and respond to potential threats as a united community, fostering a cohesive response to emergencies.
Utilizing digital platforms, such as neighborhood apps or social media groups, can provide real-time updates regarding safety concerns or unusual activities. These platforms foster a sense of community awareness and encourage residents to remain vigilant, keeping security at the forefront of everyone’s mind.
In addition to digital communication, establishing a notification chain can ensure effective responses to emergencies. Each household can designate a point of contact who swiftly relays information to neighbors, ensuring that everyone is aware of any potential threats or emergencies and can take appropriate action.
Regular community meetings can also enhance communication networks. These gatherings offer residents the opportunity to discuss security concerns, share best practices, and foster relationships that can be invaluable in times of crisis, thereby strengthening community bonds.
Collaborating with local law enforcement can further bolster communication efforts. Establishing direct lines of communication with local police departments enables residents to receive timely updates on local crime trends and strategies for prevention, enhancing community preparedness.
The importance of efficient communication cannot be overstated in ensuring community safety. By developing robust communication networks, neighborhoods can create a supportive environment that prioritizes vigilance and prepares residents for any potential emergencies.
Build Mutual Aid and Support Systems for Enhanced Resilience
Developing mutual aid and support systems within the community can significantly enhance prepper home security. These systems create a network of support and resources, ensuring that residents can rely on one another during emergencies and fostering a spirit of cooperation.
Identifying local resources is the first step in building a strong support system. This may include local businesses, community organizations, or even individual residents with specific skills. Collaborating with these entities can provide additional resources and support during crises, enhancing overall community resilience.
Establishing clear lines of communication and access to support services is essential. Residents should know who to contact for assistance during emergencies, whether it be for medical help, shelter, or other resources, ensuring that everyone feels secure and supported.
Regular community events can foster connections among residents, encouraging them to get to know their neighbors. This sense of community and trust enhances the effectiveness of mutual aid systems, as residents are more likely to seek help from those they know and trust.
Moreover, creating a community resource directory can be beneficial. This directory can include contact information for local services, volunteer opportunities, and emergency contacts, ensuring that everyone in the community has access to essential support and information.
Ultimately, mutual aid and support systems serve as valuable safety nets within communities. By fostering collaboration and resource-sharing, residents can enhance their collective security and resilience during emergencies.
Prioritize Cybersecurity and Digital Protection Measures
Secure Your Smart Home Devices Against Cyber Threats
As homes become increasingly connected through smart technology, securing these devices is crucial to maintaining a prepper’s home security. Vulnerabilities in smart home devices can provide easy access points for cybercriminals, putting your home and personal information at risk if left unprotected.
Start by assessing all smart devices in your home, including security cameras, smart locks, thermostats, and lighting systems. Ensure that each device is protected by a strong, unique password. Avoid using default passwords, which are often easily guessed and widely known, thereby increasing vulnerability to attacks.
Regularly updating your devices is crucial for maintaining security. Manufacturers frequently release firmware updates that address vulnerabilities and enhance functionality. Set a reminder to check for updates regularly or enable automatic updates whenever possible, ensuring your devices remain secure and current.
Utilizing secure Wi-Fi networks is another essential step in protecting your smart home devices. Ensure that your home network is secured with WPA3 encryption. Additionally, consider creating a separate network for your smart devices, isolating them from your main network and reducing the risk of unauthorized access to sensitive information.
Finally, educating all household members on digital safety is vital. Develop guidelines for using smart devices, such as avoiding sharing passwords or clicking on suspicious links. This knowledge empowers everyone to take an active role in maintaining their home’s digital security and safeguarding their information.
By prioritizing the security of smart home devices, homeowners can enhance their overall prepper home security strategy, safeguarding their homes against both physical and digital threats in today’s interconnected world.
Frequently Asked Questions Regarding Home Security
What components make up a prepper home security system?
A prepper home security system comprises various measures and technologies designed to protect a home from intrusions and emergencies. This includes physical barriers, surveillance systems, access control, and emergency preparedness strategies tailored to individual needs.
How can I improve my home security without spending a lot?
Enhancing home security on a budget can be achieved by reinforcing doors and windows, installing motion-sensor lights, utilizing DIY security systems, and participating in local neighborhood watch programs to strengthen community vigilance and support.
Which type of fencing is best for home security?
Durable materials, such as steel or pressure-treated wood, are ideal for home security fencing. Ensure the fence is at least six feet high, with reinforced gates and no gaps that could allow easy climbing or access, creating a secure environment.
How often should I test my security alarms?
Security alarms should be tested at least once a month to ensure they are functioning properly. Regular checks help identify any issues and provide peace of mind that your system is ready when needed, enhancing overall security.
What steps can I take to prepare for a natural disaster at home?
Preparing for a natural disaster involves creating an emergency plan, stocking essential supplies, and practicing evacuation routes to ensure safety. Regular training and community collaboration can also enhance overall preparedness and response capabilities.
What should be included in my first aid kit?
A comprehensive first aid kit should contain bandages, antiseptics, gauze, scissors, adhesive tape, pain relievers, and any specific medications required by family members, ensuring readiness for medical emergencies.
How effective are motion sensors in deterring crime?
Motion sensors are highly effective in deterring crime as they activate lighting and alarms upon detecting movement, alerting homeowners and potentially scaring off intruders before they can act, thereby significantly enhancing security.
Can smart home devices be hacked?
Yes, smart home devices can be vulnerable to hacking if not properly secured. Strong passwords, regular updates, and secure Wi-Fi networks are essential to protect against unauthorized access and maintain overall security.
What is the purpose of a safe room?
A safe room is a fortified area within a home designed for occupants to retreat to during emergencies, such as home invasions or natural disasters, providing security and protection until help arrives.
How do I start a neighborhood watch program?
To initiate a neighborhood watch program, gather interested residents, meet to discuss safety concerns, establish effective communication methods, and collaborate with local law enforcement to access resources and guidance, fostering a sense of community safety.
Explore our world on X!
The post Prepper Home Security: Essential Tips and Strategies appeared first on Survival Bite.
The Article Essential Tips and Strategies for Prepper Home Security Was Found On https://limitsofstrategy.com
-

Exit & Emergency Lighting: Essential Safety Solutions
Understanding the Vital Importance of Exit Signs in Emergencies
Research indicates that over 70% of Australians fail to notice exit signs in commercial buildings until a crisis occurs. While that small green light may seem trivial, in moments of smoke, darkness, or panic, it serves as a crucial lifeline directing individuals toward safety. Recognizing the significance of these signs can substantially improve evacuation effectiveness, establishing them as essential components of any emergency preparedness strategy.
At Direct Point Electrical, we believe that emergency and exit lighting extend beyond mere regulatory compliance; they are fundamental elements that can greatly influence life-saving actions during emergencies. Ensuring the correct installation and operational efficiency of these systems is critical for safeguarding lives.

Uncovering the Essential Roles and Importance of Exit & Emergency Lighting Systems
Exit and emergency lighting encompasses illuminated exit signs, directional indicators, and emergency pathway lights, specifically designed to remain visible when mains power is lost. These critical systems provide much-needed illumination along evacuation routes through corridors, stairwells, ramps, and exits, ensuring individuals can evacuate quickly and safely in emergencies. The availability of dependable lighting systems can significantly influence outcomes in high-stress scenarios.
These systems are not merely optional; in Victoria, strict building codes mandate that all Class 2 to Class 9 buildings must be equipped with emergency lighting that meets Australian Standard AS/NZS 2293.1. Non-compliance not only jeopardizes lives but also exposes property owners to serious legal and financial consequences, making adherence a critical aspect of effective property management.
Identifying the Serious Risks of Ignoring Emergency Lighting Maintenance
Failing to maintain emergency lighting can result in significant repercussions, such as:
- Legal penalties incurred for non-compliance with safety regulations
- Insurance complications that may arise should an incident occur
- Injury or loss of life resulting from insufficient visibility during emergency evacuations
- Reputational damage associated with safety breaches and incidents
The failure of your emergency lighting system during a crisis could lead to catastrophic outcomes. Therefore, routine inspection, testing, and maintenance are not just compliance requirements but also crucial for ensuring peace of mind among occupants and property managers alike.
Strategically Placing Emergency Lighting for Maximum Effectiveness
An effective commercial lighting system involves more than just illuminating doorways. The strategic positioning of emergency lighting is essential and should include:
- Above all designated exits
- Along escape routes, stairwells, ramps, and corridors
- At junctions where routes change direction or intersect
- Near fire extinguishers and safety equipment
- In restrooms, utility rooms, and enclosed spaces
- Throughout open-plan areas and adjacent to workstations
- Outside buildings along exit paths and in parking lots
- At every stair landing and lift lobby
- In sensitive areas such as server rooms or data centres
- In childcare, aged care, or medical facilities to assist vulnerable occupants
The unique layout of each building necessitates a customized lighting strategy—and that’s where our local expertise truly shines in delivering tailored solutions to meet your specific requirements.
Cutting-Edge Innovations in Emergency Lighting Technology
Today’s emergency lighting solutions are becoming increasingly intelligent, safer, and more energy-efficient, offering enhanced safety features that are critical during emergencies.
We specialize in installing:
- LED emergency lights that provide longevity and lower energy consumption
- Photoluminescent signs that emit light without the need for electrical power
- Directional arrow signage specifically designed for complex or multi-level buildings
- Multi-directional signs tailored for spacious open areas or various egress options
- Accessibility-compliant signs that clearly indicate wheelchair routes
These technological advancements are not merely upgrades; they are essential tools aimed at reducing confusion and expediting safe evacuations in high-stress situations where every second counts, thereby enhancing overall safety for all occupants.
The Essential Need for Regular Servicing & Maintenance of Emergency Lighting Systems
To guarantee optimal performance, emergency lighting systems require routine testing and maintenance. Victorian law mandates the following requirements:
- Monthly functional testing to confirm operational status
- Annual 90-minute battery discharge testing to ensure reliability
- Visual inspections for obstructions or damage to maintain visibility
At Direct Point Electrical, our dedicated team provides comprehensive compliance servicing, which encompasses:
- Regular testing and thorough documentation
- Battery replacements and backup solutions to ensure uninterrupted service
- Fault detection and urgent repairs to address issues efficiently
- System upgrades and layout enhancements for improved effectiveness
- Certification for compliance audits to ensure adherence to regulations
We meticulously monitor your maintenance schedule, ensuring that you are proactive in resolving potential issues before they escalate into serious problems.
Ensuring Your Exit Lights Operate Reliably When It Matters Most
Many businesses incorrectly assume that the installation of emergency lights is the final step—but without appropriate maintenance, even the most trustworthy systems can become safety liabilities. Issues such as poor placement, obstructed signage, or depleted batteries can result in devastating outcomes during emergencies.
Whether you’re outfitting a new development in Berwick, managing a retail store, or upgrading a facility with high occupancy, Direct Point Electrical brings expert knowledge and certified workmanship to every project, ensuring that safety remains the utmost priority.

Emphasizing Safety, Compliance, and Peace of Mind in Emergency Preparedness
Emergency lighting should never be regarded as an afterthought; it is your first line of defense when visibility is compromised. Moreover, it is your legal responsibility as a building owner to ensure that adequate safety measures are implemented.
We simplify the process for you, allowing you to:
- Achieve compliance with AS/NZS 2293 standards effortlessly
- Navigate council or insurance audits with confidence
- Ensure clear and safe exit paths for every occupant
- Minimize risks to your business and avoid potential penalties
Schedule Your Emergency Lighting Compliance Inspection Now
Don’t delay until a power outage reveals that your system is inadequately prepared. Contact the team at Direct Point Electrical for professional installation, testing, and maintenance of emergency lighting systems throughout Berwick and the broader Melbourne area.
We are dedicated to keeping your building compliant and ensuring the safety of your occupants at all times.
The Article: Exit & Emergency Lighting: A Lifesaving Silent Safeguard first appeared on https://writebuff.com
The Article Exit & Emergency Lighting: Your Silent Lifesaver Was Found On https://limitsofstrategy.com
-

Nuclear Fallout Shelters: Essential Protection Strategies
Comprehensive Guide to Understanding Nuclear Fallout: Assessing Risks and Preparing Responses
Exploring the Concept of Nuclear Fallout and Its Extensive Implications

Nuclear fallout signifies the perilous descent of radioactive particles back to the earth following a nuclear explosion. This critical occurrence takes place when a nuclear device detonates, releasing an explosive force that vaporizes surrounding materials and creates a cloud filled with radioactive debris. These particles can be propelled by wind, traveling vast distances and affecting areas far from the original explosion point. The primary concern associated with nuclear fallout is the severe health hazards posed by these radioactive particles. Once settled, they can contaminate soil, water, and air, thus making it imperative to comprehend the characteristics and behavior of nuclear fallout for implementing effective preparedness and safety protocols.
The fallout consists of a variety of isotopes, including cesium-137, strontium-90, and iodine-131, each exhibiting distinct half-lives that determine their hazardous presence in the environment. While some isotopes decay rapidly, others persist for decades, presenting ongoing contamination challenges. The composition and dispersion of fallout can also be influenced by the type of nuclear device employed and environmental factors, such as wind patterns. Understanding these elements is crucial for accurately evaluating risks and devising effective responses to potential nuclear emergencies.
Exploring the Health Risks Linked to Radiation Exposure from Fallout
Interacting with radiation emitted from nuclear fallout can lead to both immediate and prolonged health complications. In the short term, individuals may experience acute radiation syndrome (ARS), which presents through symptoms like nausea, vomiting, and fatigue. In extreme cases, exposure to high radiation doses can lead to fatalities. The long-term effects of such exposure are even more concerning, as it significantly heightens the risk of developing various forms of cancer, particularly leukemia and thyroid cancer. The latency period for these cancers can span from several years to decades, underscoring the critical need to understand the cumulative impacts of radiation exposure.
The vulnerability to radiation-induced diseases is not uniform across different groups; certain demographics face greater risks. For instance, children and fetuses are particularly susceptible to the detrimental effects of radiation, necessitating special considerations in emergency preparedness plans. Moreover, the psychological ramifications of radiation exposure can be profound, resulting in heightened anxiety, depression, and stress levels among affected populations. Consequently, the implementation of robust sheltering and safety protocols is essential to mitigate the health consequences linked to radiation exposure.
Understanding the Critical Role of Shelters in Nuclear Emergency Preparedness
The importance of nuclear fallout shelters cannot be overstated, especially when pondering the likelihood of nuclear events. These shelters are specifically constructed to shield individuals from the harmful effects of radioactive particles and radiation. By providing a secure environment, shelters significantly reduce exposure, allowing people to endure the immediate hazards posed by fallout. The effectiveness of a shelter largely hinges on its design and construction, emphasizing the need for radiation shielding while ensuring adequate ventilation and accessibility to essential supplies.
Establishing a shelter is a proactive measure that can greatly enhance survival chances following a nuclear incident. Governments and organizations around the globe have acknowledged the urgency of this requirement, leading to increased investment in both public and private shelters. This heightened awareness benefits individuals and cultivates a culture of preparedness, empowering communities to respond more effectively to nuclear threats. Furthermore, the psychological reassurance derived from having a secure refuge can enhance confidence during uncertain times.
Examining the Duration of Radioactive Contamination and Its Consequences

The duration of radioactive contamination following a nuclear event is influenced by various factors, including the isotopes released and prevailing environmental conditions. Different isotopes possess varying half-lives, dictating how long they remain hazardous. For example, iodine-131, with a half-life of approximately eight days, presents a short-term threat, while cesium-137 can remain dangerous for over 30 years. Understanding these timelines is vital for evaluating safety and formulating appropriate evacuation or decontamination strategies.
Environmental variables such as rainfall, wind, and temperature significantly influence how fallout disperses and settles. Heavy rainfall can wash away particles, while dry conditions may allow them to remain airborne for extended periods. Local geography, including mountains and valleys, can also shape how fallout accumulates in specific areas. Being cognizant of these factors enables the development of enhanced strategies for managing exposure and minimizing risks, ensuring communities stay informed and ready for potential nuclear incidents.
Implementing Effective Protective Measures Against Fallout
To effectively minimize exposure to nuclear fallout, various protective measures can be adopted. One of the most immediate and efficient strategies is to remain indoors, as buildings act as a barrier against radiation. Sealing windows and doors can prevent contaminated outside air containing radioactive particles from infiltrating the shelter. Additionally, wearing protective clothing, such as masks and gloves, can significantly reduce exposure for individuals who must venture outdoors.
Decontamination procedures are equally critical. If individuals come into contact with fallout, they should be instructed to promptly remove contaminated clothing and thoroughly wash themselves to eliminate radioactive particles from their skin. Understanding these protective measures can dramatically influence survival rates during a nuclear event, providing a clear pathway to safety amidst uncertainty.
Essential Blueprint for Designing Effective Nuclear Shelters
Choosing the Best Materials for Shelter Construction

Choosing appropriate construction materials is paramount in the design of nuclear fallout shelters capable of enduring the harsh realities of a nuclear explosion. Concrete and steel have been identified as two of the most effective materials for obstructing radiation. The density and thickness of these materials are vital for their ability to shield occupants from harmful radiation. For instance, several-foot-thick concrete walls can considerably diminish radiation exposure, creating a safer haven for those inside.
Moreover, the shelter design must account for possible blasts to ensure structural integrity remains intact. A well-constructed shelter, reinforced with durable materials, can offer protection not only from radiation but also from shock waves and debris generated by a nuclear blast. Incorporating multiple layers of diverse materials, such as lead or specialized radiation-resistant compounds, can further amplify protection levels, rendering the shelter more robust against various threats.
The location of the shelter is another critical aspect. Constructing underground can provide additional shielding, as the earth itself effectively blocks radiation. However, it is essential to ensure that the shelter has sufficient drainage and ventilation systems to prevent the accumulation of hazardous gases and maintain air quality.
Ensuring Effective Ventilation and Air Filtration Systems
Proper ventilation is crucial for maintaining a safe environment within nuclear fallout shelters. An effective ventilation system can expel radioactive particles from the air while supplying a continuous stream of fresh air. This requirement becomes especially critical following a nuclear event when outside air may be contaminated. Shelters should be outfitted with air filtration systems capable of capturing radioactive particulates, thereby reducing the risk of inhalation for occupants.
Advanced air filtration technologies, such as HEPA (High-Efficiency Particulate Air) filters, excel at trapping even the smallest radioactive particles, adding another layer of protection. Furthermore, shelters should incorporate redundant air exchange systems to ensure that if one system fails, another can seamlessly take its place. This redundancy is essential, as the safety of occupants may hinge on the reliability of these systems during prolonged confinement.
Natural ventilation methods, like utilizing passive air systems, can also prove beneficial. These systems leverage temperature differences to foster airflow, allowing for the exchange of stale air without compromising the shelter’s integrity. However, it is important to balance natural ventilation with security concerns, as openings could inadvertently allow contaminants to enter.
Optimizing Space and Amenities for Shelter Occupants
The design and layout of a nuclear fallout shelter should focus on maximizing space and amenities to ensure occupants’ well-being during extended confinement periods. Sufficient space is essential not only for physical comfort but also for psychological health. Overcrowding can lead to increased stress and anxiety, emphasizing the need to consider the number of individuals the shelter will accommodate relative to its size.
Amenities such as sleeping quarters, kitchen areas, and sanitation facilities significantly enhance the quality of life within the shelter. Access to fresh water and food is imperative; thus, shelters should be adequately equipped to sustain occupants for weeks or even months. Integrating recreational resources, such as books, games, and exercise equipment, can also help alleviate boredom and support mental health during periods of confinement.
Communication tools, such as radios or satellite phones, are vital for keeping occupants informed about external conditions and safety updates. Creating designated spaces for cooking, relaxation, and social interaction can help establish a sense of normalcy, easing the psychological burden of confinement. Overall, these design elements are crucial in ensuring that occupants remain physically and mentally healthy during challenging times.
Strategic Stockpiling for Comprehensive Shelter Preparedness
Establishing Robust Food and Water Reserves for Sustainability
Stockpiling an adequate supply of food and water is a fundamental aspect of preparing a nuclear fallout shelter. Non-perishable food items, such as canned goods, dried fruits, and vacuum-sealed meals, provide essential nutrients while remaining safe for extended durations. Prioritizing food that requires minimal preparation and can be consumed without cooking is advisable, as cooking facilities may be limited during confinement.
Water is arguably the most critical resource in a shelter. Each person requires at least one gallon of water per day for drinking and hygiene. Therefore, planning for a minimum of two weeks’ worth of water for each occupant is essential. This may involve storing bottled water or utilizing large water tanks that can be replenished as necessary. It is also vital to have methods for purifying water available, such as water purification tablets or filtration systems.
Regularly checking and rotating supplies is crucial to ensure that food and water reserves remain fresh and usable. Labeling items with expiration dates and developing a systematic approach for replenishing stocks can help maintain readiness. Involving all occupants in this process can foster a sense of community and shared responsibility, enhancing the shelter’s overall preparedness.
Comprehensive Medical Supplies and First Aid Kits for Emergency Care
Including a well-stocked first aid kit is an indispensable component of preparing a nuclear fallout shelter. This kit should contain essential medical supplies, such as bandages, antiseptics, and over-the-counter medications for pain relief, allergies, and digestive issues. Moreover, including specific medications for chronic conditions is critical for individuals with ongoing health needs, as access to regular medical care may be limited during emergencies.
In emergencies, having access to advanced medical equipment, such as thermometers, blood pressure monitors, and basic surgical instruments, can prove invaluable. Training occupants on how to utilize first aid supplies effectively can enhance their ability to respond to injuries and illnesses that may arise during confinement.
Furthermore, mental health resources should be considered equally important. Access to counseling materials or contact information for mental health professionals can provide necessary support during stressful times. This holistic approach to medical preparedness within the shelter creates a safety net that addresses both physical and psychological health considerations, ensuring a comprehensive response to occupant needs.
Essential Tools and Equipment for Shelter Maintenance and Functionality
Equipping a nuclear fallout shelter with essential tools and equipment is vital for maintaining the shelter’s functionality and ensuring occupant safety. Basic tools, such as flashlights, batteries, and multi-tools, should be readily available for emergencies. Flashlights are crucial for navigating low-light conditions, particularly during power outages. It is advisable to stock extra batteries to ensure the continued operation of these essential devices.
Radiation detectors are another critical piece of equipment. These devices monitor radiation levels inside and outside the shelter, providing valuable information regarding safety conditions. Knowing when it is safe to exit the shelter is paramount for the health and survival of occupants.
Moreover, tools for cleaning and sanitation, such as disinfectants, trash bags, and portable toilets, are necessary for maintaining hygiene within the shelter. Establishing a cleaning schedule can help ensure that the environment remains safe and comfortable for occupants. Lastly, leisure items such as games, books, and art supplies can alleviate boredom and help maintain a sense of normalcy during extended periods of confinement.
Prioritizing Sanitation and Hygiene Supplies for Healthy Living
Maintaining sanitation and hygiene in a nuclear fallout shelter is crucial for the health and well-being of its occupants. Stocking essential hygiene supplies, including toiletries, soap, and sanitizers, ensures individuals can maintain their cleanliness during confinement. Regular hand washing and surface cleaning are vital in preventing the spread of germs and illnesses, which can be particularly critical in confined spaces.
Effective waste management solutions, such as portable toilets or bags for human waste, are also essential. These systems should be user-friendly and easy to maintain, allowing occupants to manage waste without compromising hygiene. Having a designated area for waste disposal helps keep the shelter organized and lowers the risk of contamination.
Additionally, incorporating ventilation systems that minimize odors and moisture buildup will contribute to a more pleasant living environment. Clear communication about hygiene practices and waste management procedures can enhance compliance among occupants, ensuring that everyone actively contributes to maintaining a safe and sanitary space.
Establishing Effective Communication and Entertainment Devices for Morale
Reliable communication systems are essential in a nuclear fallout shelter for keeping occupants informed about external conditions and safety updates. Including a battery-operated or hand-crank radio enables occupants to receive emergency broadcasts and news updates regarding the situation outside. This information can significantly influence decisions regarding when it is safe to exit the shelter.
Entertainment devices also play a significant role in maintaining morale during extended confinement. Stocking games, puzzles, and books can provide necessary distractions from the stress of the situation. Creating a communal area within the shelter for these activities fosters social interaction and collaboration among occupants, which is vital for mental health and emotional well-being.
Digital devices, such as tablets or e-readers, can offer additional entertainment options, but it’s important to ensure that they are equipped with sufficient battery power or solar chargers. Balancing access to information with entertainment ensures that occupants remain engaged and informed, thereby improving their overall experience within the shelter.
Thorough Strategies for Emergency Preparedness and Response
Creating Detailed Emergency Action Plans for Shelter Occupants
Developing comprehensive emergency action plans is essential for ensuring the effectiveness of a nuclear fallout shelter. These plans should delineate specific procedures for entering the shelter, including designated routes and protocols for securing the premises. Clear communication regarding these procedures can facilitate a swift and effective response among occupants in the event of a nuclear incident.
In addition to entry procedures, plans should encompass evacuation routes and alternative shelter locations in case the primary shelter becomes compromised. Regular reviews and practice drills of these plans with all occupants can enhance preparedness, ensuring that everyone comprehends their roles during an emergency.
Moreover, tailoring action plans to meet the unique needs of occupants, including children, elderly individuals, and those with disabilities, is crucial. Addressing these diverse needs ensures that every individual can respond effectively in a crisis, bolstering confidence and cooperation among all shelter inhabitants.
Developing Robust Communication Strategies for Effective Coordination
Establishing reliable communication strategies is crucial for maintaining contact with the outside world and keeping occupants informed about safety updates. Utilizing both wired and wireless communication options, such as landline phones and radios, can provide multiple avenues for receiving critical information. Additionally, maintaining an updated list of emergency contacts, including local authorities and healthcare facilities, can facilitate swift access to assistance when required.
Regularly scheduled check-ins among shelter occupants can also help sustain a sense of connection and support. These check-ins provide opportunities to discuss concerns, share updates, and reinforce a sense of community during challenging times. Designating communication leaders within the shelter can streamline this process, ensuring that information flows efficiently and effectively.
Furthermore, establishing a communication plan that considers potential factors affecting connectivity, such as power outages or severe weather conditions, is crucial. Implementing backup systems for communication, such as solar-powered devices, can enhance reliability, allowing occupants to remain informed even in adverse situations.
Conducting Regular Training and Drills for Preparedness
Regular training and drills are fundamental in ensuring that all occupants of a nuclear fallout shelter can respond effectively during a nuclear event. Conducting periodic drills familiarizes everyone with shelter procedures, paving the way for a smooth and organized response when needed. These drills should cover various scenarios, including evacuation, shelter entry, and communication protocols, allowing occupants to practice and refine their skills.
Training should also focus on educating occupants about radiation safety, including strategies to minimize exposure and recognize signs of contamination. This knowledge equips individuals with the necessary tools to make informed decisions during critical moments, thereby enhancing their overall safety and preparedness.
Additionally, creating opportunities for occupants to discuss their roles during drills can foster teamwork and collaboration. Encouraging open communication about concerns and questions can lead to improved preparedness and planning, ultimately enhancing the shelter’s effectiveness in a real emergency.
Maintaining Ideal Conditions in Nuclear Shelters
Conducting Regular Inspections for Safety and Readiness
Performing regular inspections of a nuclear fallout shelter is crucial for ensuring its readiness and safety. These inspections should involve assessing structural integrity, ventilation systems, and stock supplies. Any signs of wear or damage must be promptly addressed to prevent more significant issues from developing.
In addition to physical inspections, it is imperative to routinely test equipment, including air filters, communication devices, and radiation detectors. Ensuring the functionality of these critical systems can significantly impact the shelter’s overall effectiveness in an emergency. A well-maintained shelter can greatly enhance the safety and comfort of its occupants during challenging circumstances.
Documenting inspection findings and any corrective actions taken is also beneficial. This record can aid in tracking maintenance over time and facilitate more effective planning for future inspections. Engaging all occupants in the inspection process can foster a sense of ownership and responsibility, thereby enhancing the overall preparedness of the shelter.
Updating and Refreshing Supplies Regularly for Sustained Readiness
Regularly updating and replenishing supplies in a nuclear fallout shelter is a key aspect of maintaining readiness. Food, water, and medical supplies should be rotated to ensure that items remain fresh and within their expiration dates. Establishing a systematic schedule for updating supplies can help ensure that nothing is overlooked, promoting a culture of preparedness and vigilance.
In addition to food and water, it is essential to periodically review the inventory of tools and equipment. Ensuring that essential items are available and in good working condition can facilitate the smooth operation of the shelter in emergencies. This includes checking batteries, replacing expired medications, and restocking hygiene supplies as necessary to ensure continued functionality and safety.
Involving occupants in supply management can enhance engagement and instill a sense of responsibility. Assigning specific tasks or areas of focus can help ensure that everyone contributes to the shelter’s overall preparedness, fostering teamwork and collaboration among all inhabitants.
Effectively Addressing Contamination Risks Within the Shelter
Implementing protocols for addressing contamination within a nuclear fallout shelter is vital for ensuring the safety of occupants. In the event of radiation exposure, clear procedures must be in place for decontaminating both the shelter and its inhabitants. This may involve removing contaminated clothing and utilizing decontamination supplies to cleanse skin and surfaces effectively.
Alongside immediate decontamination, developing long-term protocols for monitoring radiation levels within the shelter is essential. Regular testing can help identify any lingering contamination, enabling appropriate actions to be taken. This monitoring should be integrated into the regular inspection process to ensure ongoing safety and preparedness.
Providing education and training on contamination protocols empowers occupants to respond effectively in a crisis. This knowledge enhances individual safety and promotes a collective responsibility for maintaining a secure shelter environment, contributing to the well-being of all inhabitants.
Addressing Psychological Considerations in Shelter Confinement
Strategies for Managing Stress and Anxiety in Shelter Environments
The psychological impact of confinement in a nuclear fallout shelter can be significant, making effective strategies for managing stress and anxiety essential. Providing resources and support for occupants can aid individuals in coping with the emotional strain of a nuclear event. Creating an environment of open communication allows occupants to share their feelings and concerns, fostering a sense of community and mutual support.
Incorporating relaxation techniques, such as deep breathing exercises and mindfulness practices, can assist individuals in managing anxiety levels. Designating quiet areas within the shelter for meditation or reflection promotes emotional well-being, allowing occupants to find moments of peace during the chaos of confinement.
Moreover, engaging in physical activity, even within confined spaces, can alleviate stress and boost overall morale. Encouraging occupants to participate in group exercises or stretches fosters camaraderie while benefitting mental health. By addressing psychological needs, shelters can enhance the overall resilience and well-being of their inhabitants during difficult times.
Incorporating Activities to Enhance Mental Health and Well-Being
Integrating activities that promote mental health is vital for sustaining morale within a nuclear fallout shelter. Recreational options, such as board games, puzzles, and books, provide necessary distractions and encourage social interaction among occupants. These activities can keep minds engaged and reduce feelings of isolation and anxiety, positively affecting the overall atmosphere within the shelter.
Organizing group activities, like storytelling sessions or arts and crafts, can further strengthen the sense of community. These shared experiences create lasting memories and bonds among occupants, making the confinement experience more manageable. Emphasizing collaboration in activities can also foster teamwork, enhancing the overall atmosphere and camaraderie within the shelter.
In addition to structured activities, providing resources for individual pursuits, such as journaling or creative writing, can offer an outlet for personal expression. Encouraging occupants to document their experiences can provide therapeutic benefits, allowing individuals to process their emotions during challenging times.
Building Community and Support Systems for Psychological Resilience
Fostering a sense of community and support is crucial for psychological resilience within a nuclear fallout shelter. Creating opportunities for social interaction among occupants enhances feelings of safety and belonging. Regular group discussions, sharing meals, or participating in group activities can promote emotional connections and strengthen relationships among all individuals in the shelter.
Designating support roles within the shelter can also enhance community dynamics. Assigning individuals specific responsibilities, such as leading activities or providing emotional support, fosters a sense of purpose and ownership among occupants. This structure helps cultivate a supportive environment where individuals feel valued and appreciated, thereby boosting overall morale.
Additionally, establishing communication channels for expressing concerns or sharing experiences can further promote social cohesion. Providing regular check-ins or feedback sessions allows occupants to express their needs and feelings, thereby reinforcing a supportive atmosphere. By nurturing a strong sense of community, shelters can enhance the psychological resilience of their inhabitants during confinement.
Facilitating Access to Mental Health Professionals for Support
Ensuring access to mental health professionals for consultations and therapy sessions is crucial for addressing the psychological needs of occupants in a nuclear fallout shelter. Having trained professionals available to provide support can help individuals navigate the emotional challenges that arise during confinement. This support is particularly vital for those experiencing heightened anxiety, distress, or trauma.
Establishing a system for mental health check-ins can facilitate regular contact with professionals, allowing occupants to discuss their feelings and concerns openly. Workshops or sessions focusing on stress management, coping strategies, and emotional resilience can also provide valuable resources for maintaining mental health and well-being during this critical time.
Additionally, providing information about mental health resources outside the shelter can help occupants feel connected to the broader community. Maintaining a list of local mental health services and support groups can ease access to assistance once it is safe to leave the shelter. By prioritizing mental health, shelters can enhance the well-being of their inhabitants, ensuring they are better equipped to face forthcoming challenges.
Long-Term Survival Strategies for Shelter Occupants
Implementing Sustainable Living Practices for Extended Survival
Planning for sustainable living within a nuclear fallout shelter is essential for ensuring long-term survival. This involves considering renewable energy sources, such as solar panels or wind turbines, to provide power for essential systems while decreasing reliance on external resources. Additionally, integrating systems for collecting rainwater or purifying wastewater can enhance sustainability, ensuring a steady supply of clean water for all occupants.
Moreover, incorporating gardening methods, such as hydroponics or aquaponics, allows occupants to cultivate fresh food within the shelter. These systems are not only space-efficient but also deliver essential nutrients during extended confinement periods. Educating occupants about these sustainable practices empowers them to take an active role in their survival and well-being.
Lastly, effective waste management systems are critical for maintaining a healthy environment. Implementing composting solutions and recycling programs can minimize waste and promote a cleaner living space. By fostering a culture of sustainability, shelters can improve the overall quality of life for their inhabitants while preparing for long-term survival in the face of nuclear threats.
Strategies for Re-establishing Communication After a Nuclear Incident
Developing strategies for safely re-establishing contact with the outside world after a nuclear event is vital for occupants of a nuclear fallout shelter. As conditions stabilize, having a clear plan for communication can facilitate access to vital information and resources. This may include using radios to receive updates from emergency services or local authorities regarding the situation outside.
Establishing a timeline for when it is safe to exit the shelter is crucial. Monitoring radiation levels with detection equipment can help determine when conditions have improved sufficiently. Additionally, creating protocols for safe travel, including identifying secure routes and potential hazards, can enhance the safety of occupants as they navigate the post-event landscape.
Moreover, encouraging occupants to maintain a list of contacts and resources outside the shelter can facilitate the re-establishment of community connections. Knowing whom to reach out to for assistance or support can help individuals transition back into their lives after confinement. By prioritizing communication and safety, shelters can help occupants navigate the complexities of re-establishing contact with the outside world.
Planning for Future Challenges and Recovery After Shelter Confinement
Considering long-term survival plans is essential for occupants of a nuclear fallout shelter. This involves developing exit strategies that account for potential long-term effects of a nuclear event, such as environmental contamination or infrastructure damage. Preparing occupants for the realities they may encounter upon leaving the shelter can enhance their resilience and adaptability in a changing world.
Additionally, creating a plan for rebuilding efforts can provide a sense of hope and purpose. Encouraging occupants to contemplate their goals and aspirations for the future can foster a positive mindset during challenging times. Establishing a community action plan for recovery can help individuals feel empowered to contribute to rebuilding efforts once it is safe to do so.
Furthermore, emphasizing the importance of community support and collaboration can facilitate the rebuilding process. Encouraging occupants to connect with local organizations and resources can enhance their ability to navigate recovery challenges effectively. By focusing on long-term survival and community resilience, shelters can help occupants prepare for a brighter future beyond confinement.
Understanding Legal and Ethical Considerations in Shelter Preparedness
Navigating the Legal Framework for Constructing and Operating Shelters
Understanding the legal framework surrounding the construction and operation of nuclear fallout shelters is essential for ensuring compliance with safety regulations and local laws. Various countries have established codes and standards that govern shelter design and construction, including building codes and zoning laws. Familiarizing oneself with these regulations can ensure that shelters are built to withstand potential nuclear incidents while providing adequate protection for occupants.
Moreover, liability considerations are crucial for shelter owners and operators. Establishing clear guidelines for the usage and management of shelters can help mitigate legal risks during emergencies. Additionally, securing appropriate insurance coverage can provide financial protection against potential claims arising from shelter occupancy and use.
It is also vital to consider the ethical implications of shelter ownership and access. Ensuring equitable access to shelters, particularly for vulnerable populations, is a fundamental aspect of ethical preparedness. Exploring community-based solutions and collaborative efforts can help ensure that those most in need have access to safe shelter during nuclear incidents, fostering a more just and inclusive approach to emergency preparedness.
Exploring Ethical Considerations in Emergency Preparedness Initiatives
The ethical considerations surrounding emergency preparedness in the context of nuclear fallout shelters are multifaceted. Prioritizing the safety and well-being of all individuals, regardless of socioeconomic status, is paramount. This involves addressing disparities in access to resources and ensuring that marginalized communities are included in preparedness initiatives.
Furthermore, transparency in communication and decision-making processes is vital for building trust within communities. Engaging stakeholders in discussions about shelter planning and operation can foster a sense of ownership and responsibility, enhancing overall preparedness. Ethical considerations also extend to the treatment of individuals in shelters, emphasizing the importance of respect, dignity, and support during challenging times.
Ultimately, addressing these ethical dilemmas requires a commitment to social justice and equity in emergency preparedness and response. By prioritizing inclusivity and community engagement, preparations for nuclear events can be more effective and just, ensuring that all individuals have the resources they need to protect themselves and their families.
The Impact of Government Policies on Enhancing Shelter Preparedness
Government policies significantly shape the landscape of nuclear fallout shelters and emergency preparedness. Establishing clear guidelines for shelter construction, maintenance, and usage can enhance community safety and resilience. Governments can also provide resources and funding to support public awareness campaigns about the importance of preparedness and available shelter options.
Furthermore, developing partnerships between government agencies and local organizations can facilitate community-based preparedness initiatives. Collaborative efforts can help address the specific needs of diverse populations, ensuring equitable access to resources and support during emergencies. Training programs for citizens, emphasizing radiation safety and emergency response, can empower individuals to take charge of their safety and well-being.
Additionally, government support for research and innovation in shelter design and emergency response technologies can enhance overall preparedness and resilience. Encouraging advancements in materials, ventilation systems, and sanitation solutions can create safer and more comfortable living conditions for occupants. By prioritizing these policies and initiatives, governments can play a pivotal role in fostering resilience and safety in the face of nuclear threats.
Frequently Asked Questions Regarding Nuclear Fallout Shelters
What are nuclear fallout shelters and what purpose do they serve?
Nuclear fallout shelters are specially designed structures intended to protect occupants from harmful radiation and radioactive particles following a nuclear explosion. They provide a secure environment to endure the immediate dangers posed by fallout, thereby minimizing radiation exposure.
How do nuclear fallout shelters function to ensure the safety of occupants?
Nuclear fallout shelters operate by utilizing dense construction materials, such as concrete and steel, to block harmful radiation. They typically include ventilation and air filtration systems to maintain air quality, effectively safeguarding occupants from contaminated air.
What essential supplies should I prepare for my fallout shelter?
Essential supplies for a fallout shelter encompass non-perishable food, sufficient water, first aid kits, sanitation items, tools, and entertainment devices. It is crucial to ensure there are adequate provisions to sustain occupants for several weeks or even months.
What steps can I take to effectively prepare for emergencies related to nuclear fallout?
Preparing for nuclear fallout involves creating a comprehensive emergency action plan, establishing robust communication strategies, and conducting regular drills to familiarize occupants with shelter protocols and procedures for an effective response.
What psychological support resources can be accessed in fallout shelters?
Accessing mental health professionals and resources to manage stress and anxiety is vital. Additionally, engaging in activities that promote social interaction and mental well-being contributes to creating a supportive environment within the shelter.
How long can radioactive contamination persist following a nuclear incident?
The duration of radioactive contamination varies based on the isotopes involved. Some isotopes decay rapidly, while others can remain hazardous for years, making careful planning and ongoing monitoring of radiation levels essential to ensure safety.
What legal considerations must I address when constructing a fallout shelter?
Legal considerations for building a fallout shelter include compliance with local building codes, addressing liability issues, and adhering to regulations governing shelter access and operation to ensure safety and legal protection.
How can communities ensure equitable access to fallout shelters?
Communities can ensure equitable access to fallout shelters by actively engaging diverse populations in preparedness planning, addressing disparities in resources, and providing support for vulnerable individuals to ensure everyone has access to a safe shelter during nuclear incidents.
What role do governments play in enhancing emergency preparedness?
Governments play a crucial role in emergency preparedness through policies that guide shelter construction, fund public awareness initiatives, and support research and innovation in safety technologies to enhance community resilience.
How can I ensure my fallout shelter is adequately prepared for emergencies?
To ensure your fallout shelter is ready for use, conduct regular inspections, update supplies as needed, and involve all occupants in maintenance and preparedness efforts. Maintaining the shelter in optimal condition is crucial for its effective use during emergencies.
Explore our journey on X!
The post Nuclear Fallout Shelters: Essential Protection Strategies appeared first on Survival Bite.
The Article Nuclear Fallout Shelters: Key Strategies for Essential Protection Was Found On https://limitsofstrategy.com
-

DDoS Protection: Essential Tips for Choosing Hosting Solutions
Comprehensive Analysis of DDoS Attacks and Their Impact on Online Services
Exploring the Mechanics of DDoS Attacks: How They Operate and Their Consequences

A DDoS (Distributed Denial of Service) attack represents a malicious strategy aimed at disrupting the typical operations of a targeted server, service, or network by inundating it with an excessive amount of Internet traffic. This flood of requests can lead to a complete inability for legitimate users to access websites, posing significant threats to businesses that rely on their online presence for success. In today’s digital landscape, where maintaining a robust online footprint is crucial, grasping the intricacies of DDoS attacks is vital for anyone aiming to protect their websites effectively. When selecting hosting solutions, it is imperative to opt for providers that offer substantial how to choose hosting with ddos protection features designed to withstand such disruptive assaults.
The operational mechanics of a DDoS attack are surprisingly straightforward but can lead to disastrous outcomes. Typically, cybercriminals exploit a network of compromised devices, termed a “botnet,” to execute these attacks. Each infected device inundates the target with numerous requests, generating a traffic surge that legitimate users find impossible to navigate. This unrelenting assault can result in substantial downtime, severe financial losses, and a detrimental impact on a company’s reputation in its respective industry.
Understanding DDoS attacks goes beyond merely recognizing their definition; it is crucial to acknowledge that these attacks can manifest in a variety of forms. Attackers continually refine their methods, making it essential for hosting providers to proactively address emerging threats by employing effective DDoS protection strategies. Acquiring a thorough understanding of how these attacks unfold will empower you to make informed decisions as you navigate how to choose hosting with ddos protection.
Diverse Types of DDoS Attacks: Detailed Breakdown and Protective Measures
DDoS attacks manifest in several varieties, each engineered to exploit distinct elements of network protocols and applications. The primary categories include volumetric attacks, protocol attacks, and application layer attacks. Comprehending these distinctions is critical for deploying appropriate protective strategies when investigating how to choose hosting with ddos protection.
Volumetric attacks represent the most prevalent type, focusing on overwhelming the target’s bandwidth with excessive traffic. Techniques such as UDP floods and ICMP floods are frequently employed, generating massive data volumes that can surpass the server’s capacity. To effectively defend against volumetric attacks, it is often necessary to utilize specialized hardware and software solutions adept at filtering out illegitimate traffic before it reaches the server.
Conversely, protocol attacks take advantage of vulnerabilities within network protocols, such as SYN floods or Ping of Death. Unlike volumetric attacks, these do not necessarily rely on generating high traffic volumes; instead, they disrupt service by consuming server resources or exploiting weaknesses within the network infrastructure itself. Implementing a combination of robust firewall configurations and protocol anomaly detection can substantially mitigate these risks.
Application layer attacks are particularly insidious, as they specifically target web application components and exploit weaknesses in HTTP requests. These attacks often masquerade as legitimate user traffic, complicating detection. For example, an HTTP flood can inundate a server with requests that appear normal yet ultimately overwhelm the application layer. To safeguard against these attacks, sophisticated defenses, including web application firewalls and traffic analysis tools, are imperative.
Grasping these various attack types is pivotal when determining how to choose hosting with ddos protection. Each type necessitates a tailored security approach, ensuring that your selected hosting provider can effectively counteract the specific threats your website may encounter.
Assessing the Far-Reaching Consequences of DDoS Attacks on Businesses
The fallout from DDoS attacks is extensive, with potentially catastrophic implications for businesses and organizations across the globe. A successful DDoS attack not only results in immediate service interruptions but also leads to long-term consequences, including financial losses, reputational damage, and diminished customer trust. Recognizing the impacts of these attacks is crucial for making well-informed choices regarding how to choose hosting with ddos protection.
When a website becomes unreachable due to a DDoS attack, the immediate financial ramifications can be substantial, particularly for e-commerce platforms. Even a few hours of downtime can equate to significant revenue losses. Additionally, the financial fallout extends beyond immediate revenue drops; recovery costs, which may involve enhancing security measures and compensating affected customers, can escalate quickly.
Reputational damage represents another critical risk linked to DDoS attacks. In our interconnected world, negative customer experiences can swiftly spread through social media platforms and online reviews. A DDoS attack may foster a perception of vulnerability, prompting customers to seek more reliable alternatives. This erosion of consumer confidence can have lasting effects on a brand’s reputation, complicating the recovery process.
To mitigate these adverse consequences, businesses must emphasize strong DDoS protection strategies and consider related costs when selecting hosting solutions. By understanding the potential repercussions of DDoS attacks, you can make more informed decisions regarding how to choose hosting with ddos protection, ensuring your organization remains resilient against these increasingly prevalent threats.
Formulating Effective Strategies to Prevent DDoS Attacks

Preventing DDoS attacks necessitates a proactive and multifaceted approach that encompasses various layers of security measures. As the frequency and sophistication of these attacks continue to grow, organizations must implement robust preventive strategies to protect their online assets effectively. This strategy should integrate a combination of firewalls, load balancers, and specialized DDoS mitigation services, which are essential components of a comprehensive defense against malicious traffic.
Firewalls function as the initial line of defense against unwanted traffic. By establishing stringent rules and filters, they can identify and block traffic that deviates from expected patterns. However, relying solely on basic firewall solutions is insufficient. As attackers become more sophisticated, conventional firewalls can reveal significant vulnerabilities. Advanced firewalls that scrutinize packet details and distinguish between legitimate and harmful traffic are vital for effective protection.
Load balancers play a crucial role in distributing incoming traffic across multiple servers. By efficiently allocating the load, these devices can help mitigate the effects of a DDoS attack on any single server. A well-configured load balancing solution ensures that even during peak traffic incidents, genuine users can access the website, preserving service continuity and minimizing the likelihood of server overload.
In addition to these measures, investing in dedicated DDoS mitigation services can provide an extra layer of protection. These services typically employ thorough traffic analysis, identifying and filtering suspicious traffic patterns before they reach the intended target. Many hosting providers now offer integrated DDoS protection solutions as part of their service packages, simplifying the process for businesses to enhance their defenses without incurring substantial additional costs.
As you navigate your way toward how to choose hosting with ddos protection, understanding the importance of these preventive strategies is essential. By implementing a comprehensive approach that combines firewalls, load balancers, and specialized DDoS mitigation services, you can significantly reduce the risk of falling victim to an attack, ensuring your online services remain available to users at all times.
Planning Your Response Strategy for DDoS Attacks
Despite having implemented the best preventive measures, DDoS attacks may still occur. Thus, possessing a well-defined incident response plan is crucial for organizations aiming to mitigate the impact of an attack swiftly. This plan should outline a series of predefined actions to take upon detecting an attack, ensuring that the response is both rapid and effective.
The initial step in responding to a DDoS attack is conducting thorough traffic analysis. By closely monitoring network traffic, organizations can identify unusual patterns that may indicate the onset of an assault. This analysis not only aids in understanding the nature of the attack but also informs the most effective response measures. Utilizing real-time analytics tools can significantly enhance this process, enabling immediate adjustments to traffic filtering rules as attack patterns evolve.
Once the attack is identified, the next step involves rapid mitigation. This entails deploying pre-configured defensive measures to quickly lessen the attack’s impact. For instance, if a volumetric attack is detected, network engineers can activate additional bandwidth and reroute traffic through scrubbing services that filter out harmful requests.
Furthermore, maintaining communication with stakeholders during a DDoS attack is vital. Keeping customers, employees, and partners informed can help manage expectations and sustain trust. Transparency regarding the situation and the steps being taken to resolve it can reinforce the organization’s commitment to service reliability and customer satisfaction.
In the complex landscape of online security, understanding how to choose hosting with ddos protection transcends mere prevention; it requires a robust response strategy. By developing a comprehensive incident response plan, your organization can significantly mitigate the impact of DDoS attacks, ensuring resilience in the face of persistent threats.
Essential Features of Effective DDoS Protection Services
Employing Advanced Traffic Filtering Techniques for Robust Defense

At the heart of effective DDoS protection lies advanced traffic filtering, a mechanism designed to differentiate between legitimate and harmful traffic. Given the rising sophistication of cyber threats, hosting providers must adopt robust filtering techniques to safeguard their clients’ online assets. An effective filtering system ensures that only valid requests reach the server while blocking harmful traffic that could disrupt services.
Traffic filtering typically operates across multiple layers of the network stack. This multi-layered approach enables the detection and blocking of various attack types, whether they originate from botnets or target application vulnerabilities. By analyzing incoming traffic patterns and behaviors, advanced filtering systems can identify unusual spikes or patterns indicative of an ongoing DDoS attack.
Moreover, leveraging machine learning algorithms can significantly enhance the effectiveness of traffic filtering. These algorithms continuously learn from new traffic patterns, dynamically adjusting filtering rules in real time to adapt to evolving attack vectors. This proactive approach dramatically improves the chances of detecting and neutralizing threats before they can compromise service availability.
When considering how to choose hosting with ddos protection, pay close attention to the traffic filtering capabilities of potential providers. A hosting solution that incorporates sophisticated filtering techniques not only shields your website from DDoS attacks but also boosts overall performance by ensuring that server resources are allocated efficiently, focusing on legitimate traffic.
Ensuring Scalability for Comprehensive DDoS Protection
Scalability is a crucial feature in DDoS protection, ensuring that hosting solutions can adapt to varying levels of traffic, particularly during an attack. The capability to scale resources up or down in real-time allows organizations to maintain service availability, even under heavy traffic loads. This flexibility is particularly vital in an environment where online demand can unexpectedly surge due to marketing campaigns, viral content, or unfortunately, DDoS attacks.
An effective, scalable DDoS protection solution should seamlessly adjust to traffic fluctuations, allocating additional bandwidth or processing power as needed. For instance, during a DDoS attack, a scalable system can automatically augment resources to handle the influx of malicious requests, safeguarding legitimate users while preserving website functionality.
Additionally, businesses must consider the types of scalability offered by hosting providers. Some solutions may provide only horizontal scalability, where additional devices or servers are added to distribute the load. Others might offer vertical scalability, allowing for upgrades of existing server resources. The ideal hosting solution will provide both types of scalability to ensure comprehensive protection against DDoS attacks.
When exploring how to choose hosting with ddos protection, examine the scalability options available from potential providers. A hosting solution that can efficiently manage traffic spikes and adapt to shifting demands is essential for keeping your online presence secure and accessible, minimizing the risk of downtime during critical periods.
Implementing Real-Time Monitoring Systems for Proactive Defense
Real-time monitoring is a critical component of effective DDoS protection, providing organizations with immediate visibility into their network traffic. By continuously analyzing incoming requests and user behavior, businesses can swiftly detect potential threats and initiate timely responses to mitigate any impact. This proactive approach is vital for maintaining service availability in a landscape where DDoS attacks are becoming increasingly common.
Sophisticated monitoring solutions utilize advanced analytics to identify anomalies in traffic that may signify an ongoing attack. These systems can alert network administrators in real time, enabling them to take immediate action to counteract the threat. For example, if an unusual spike in traffic is detected, network engineers can implement filtering protocols to block malicious requests before they affect server performance.
Moreover, employing dashboards that provide visual insights into network activity can enhance situational awareness. These dashboards can display critical metrics such as traffic volume, connection rates, and potential attack vectors, facilitating informed decision-making in response to emerging threats.
When considering how to choose hosting with ddos protection, prioritize providers that offer comprehensive real-time monitoring solutions. The ability to detect and respond rapidly to DDoS attacks can significantly enhance your organization’s resilience, ensuring that your website remains operational and accessible to legitimate users at all times.
Automating Mitigation Strategies for Enhanced Security
Automated mitigation systems are becoming increasingly essential in the fight against DDoS attacks. These advanced solutions can respond to threats in real time without requiring manual intervention, significantly reducing response times and minimizing potential damage. Implementing automated mitigation strategies allows hosting providers to offer businesses peace of mind, ensuring their online presence is consistently protected.
Automated mitigation typically employs predefined rules and actions triggered in response to specific attack patterns. For instance, if a volumetric attack is detected, the system may automatically reroute traffic through scrubbing centers that filter out harmful requests while allowing legitimate traffic to pass through. This rapid action helps maintain service availability, even during critical attack periods.
Moreover, modern automated systems frequently incorporate artificial intelligence (AI) and machine learning technologies to enhance their effectiveness. These systems analyze vast amounts of data to identify emerging threats and learn from past incidents, continuously improving their response strategies. This adaptability is crucial, as DDoS attack methods evolve rapidly, making it essential for protection mechanisms to keep pace.
When exploring how to choose hosting with ddos protection, evaluate the automated mitigation capabilities offered by potential providers. A hosting solution with robust automated systems can significantly enhance your organization’s ability to respond to DDoS threats, ensuring that your website remains secure and operational in the face of adversity.
Key Considerations for Choosing the Right Hosting Providers
Assessing the Reputation and Reliability of Hosting Services
When selecting a hosting provider, the reputation and reliability of that provider should be paramount in your considerations. The hosting market is saturated, but not all providers deliver the same level of service regarding DDoS protection. Researching the track record of potential providers, including their uptime history and customer satisfaction ratings, is essential for making an informed decision on how to choose hosting with ddos protection.
One effective method for gauging a hosting provider’s reputation is to read online reviews and testimonials. Engaging with current and former customers can yield valuable insights into their experiences with DDoS protection and overall service quality. Additionally, look for providers recognized within the industry for their reliability and innovative security solutions.
Another crucial aspect to consider is the provider’s history in responding to DDoS attacks. A reputable hosting provider will often have documented case studies showcasing their ability to effectively mitigate attacks. This evidence not only demonstrates their technical capabilities but also reflects their commitment to maintaining service reliability for their clients.
In your search for robust DDoS protection, prioritize hosting providers with a strong reputation for reliability. By opting for a provider that has consistently demonstrated effective DDoS defense measures, you can significantly reduce your risk of downtime and maintain the integrity of your online services.
Prioritizing Customer Support in Hosting Services
Reliable customer support is a critical factor when evaluating hosting providers, particularly regarding DDoS protection. When an attack occurs, having access to knowledgeable support staff can make a significant difference in resolving issues quickly and effectively. Therefore, it’s essential to choose a hosting provider that offers robust customer support available around the clock.
Look for hosting providers that offer multiple channels for customer support, including live chat, phone support, and ticketing systems. This accessibility ensures that you can reach out for assistance at any time, regardless of your location. Additionally, seek out providers with a reputation for responsiveness and thoroughness in their support interactions.
In the event of a DDoS attack, swift assistance is crucial. A provider with experienced technical support staff can help you implement immediate defensive measures, analyze the attack, and adjust settings as necessary. This rapid response capability is vital for minimizing downtime and maintaining service availability during a crisis.
As you explore how to choose hosting with ddos protection, make customer support a key factor in your decision-making process. A hosting provider with excellent support services will enhance your experience while providing peace of mind, knowing that expert assistance is available whenever needed.
Understanding Service Level Agreements (SLAs) and Their Importance
Service Level Agreements (SLAs) are crucial documents outlining the expected level of service provided by hosting companies, including their commitments regarding uptime, performance, and DDoS protection. When evaluating providers, scrutinizing SLAs can help you assess their dedication to maintaining security and stability for your website.
SLAs typically include specific metrics related to uptime, often expressed as a percentage. Look for providers that guarantee uptime of 99.9% or higher, as this reflects their capacity to mitigate DDoS attacks effectively. Providers that commit to high uptime levels are likely to have implemented advanced DDoS protection measures, ensuring minimal disruption to your services.
Furthermore, SLAs should detail the provider’s responsibilities in the event of a DDoS attack or other service disruptions. Understanding the compensation or remediation measures in place can provide added reassurance that the provider takes their commitments seriously. This clarity is especially critical for businesses that depend on their online presence for revenue generation.
As you consider how to choose hosting with ddos protection, pay close attention to the SLAs offered by potential providers. A comprehensive and transparent SLA can serve as a strong indicator of the provider’s reliability and commitment to safeguarding your online assets.
Evaluating Pricing Structures and Hosting Plans
When assessing hosting providers for DDoS protection, it is vital to consider pricing and plans to ensure you receive value for your investment. While cost is undoubtedly a significant factor, balancing your budget constraints with the need for robust security measures to protect your online presence is crucial.
Different hosting providers may offer a variety of pricing models, such as monthly subscriptions, pay-per-use, or tiered plans that scale based on your needs. Take the time to compare these options, considering the level of DDoS protection included in each plan. Some providers may offer basic protection at lower price points, while others might include comprehensive security features as standard.
Additionally, be mindful of potential hidden costs that could arise. Some providers may charge extra for high-traffic periods or require setup fees for advanced DDoS protection measures. Understanding the full scope of pricing will help you make informed decisions and avoid unexpected expenses down the line.
While evaluating how to choose hosting with ddos protection, invest in a provider that offers a pricing structure meeting your budgetary needs while still delivering robust DDoS protection. A well-structured plan can provide significant peace of mind, allowing you to focus on growing your business without the constant worry of potential attacks.
Addressing Scalability and Performance in Hosting Solutions
Scalability and performance are vital considerations when selecting a hosting provider, particularly concerning DDoS protection. The ability to manage sudden spikes in traffic without compromising performance is critical for maintaining service availability, especially during attacks.
A scalable hosting solution should facilitate dynamic resource allocation, ensuring your website can adapt to fluctuating demands. This means that whether you’re experiencing a temporary traffic surge from a successful marketing campaign or facing a DDoS attack, your hosting provider should have the capability to deliver the necessary resources to maintain performance.
In addition to scalability, the overall performance of the hosting infrastructure is paramount. Look for providers that utilize high-performance hardware, advanced network configurations, and optimized server environments to enhance load times and user experiences. A well-performing site is better equipped to withstand DDoS attacks, as the infrastructure will have greater capacity to absorb incoming traffic.
Ultimately, when exploring how to choose hosting with ddos protection, prioritize providers that offer robust scalability and performance features. Selecting a hosting solution capable of efficiently handling traffic spikes while delivering high-quality performance will ensure that your online presence remains secure and accessible, even during challenging circumstances.
Understanding Cost Considerations in DDoS Protection
Examining Various Pricing Models for DDoS Protection
When selecting a hosting provider offering DDoS protection, understanding pricing models is crucial for ensuring you receive the best value for your investment. Different providers may present various pricing structures, including monthly subscriptions, pay-as-you-go options, or tiered plans, each catering to different needs and budgets.
Monthly subscriptions often provide predictable costs, allowing businesses to budget effectively for their hosting expenses. However, it’s vital to ensure that these plans encompass adequate DDoS protection features, as some low-cost options may skimp on essential security measures. Comparing the offerings of multiple providers can help you find a plan that balances affordability with comprehensive protection.
Conversely, pay-as-you-go pricing models can be beneficial for businesses experiencing fluctuating traffic levels. This model allows you to pay solely for the resources you consume, which can be cost-effective during periods of low traffic. However, businesses should remain vigilant, as costs can escalate rapidly during high-traffic periods or when under attack.
Tiered pricing plans often provide a hybrid approach, allowing you to select a package that best suits your needs. These plans may include varying levels of DDoS protection, enabling you to upgrade as your business expands. This flexibility can be particularly advantageous for organizations with long-term growth plans.
As you consider how to choose hosting with ddos protection, closely examine the pricing models available from potential providers. Understanding the nuances of each option will empower you to make informed decisions, ensuring you receive adequate protection without exceeding your budget.
Identifying Hidden Costs in Hosting Plans
When evaluating hosting plans, hidden costs can often catch businesses off guard, particularly concerning DDoS protection. It’s essential to be aware of potential additional charges that may arise, as these can significantly affect your overall budget and return on investment.
One common hidden cost is the setup fee that some providers may charge for implementing DDoS protection measures. This fee can vary widely among hosting providers, so it’s crucial to inquire upfront about any initial costs associated with establishing your hosting account. Additionally, some providers may impose charges for certain features or add-ons not included in the base plan.
Another area to watch for is costs related to high-traffic periods. Many hosting providers enforce policies that throttle bandwidth usage or impose additional charges during traffic spikes, particularly during DDoS attacks. Understanding the terms of these policies can help you anticipate and manage potential costs.
Lastly, consider any potential penalties for exceeding resource limits, as these can impose additional financial strain during busy periods. Clear communication with potential providers will help you identify any hidden costs associated with their services, ensuring you can budget effectively.
In your quest for how to choose hosting with ddos protection, conducting thorough research to uncover any potential hidden costs is imperative. By acquiring this knowledge, you can avoid unexpected expenses and make informed decisions regarding your hosting and DDoS protection needs.
Strategizing Your Budget Planning for DDoS Protection
Effective budget planning is crucial for organizations seeking reliable DDoS protection through their hosting provider. As businesses navigate the competitive online landscape, it’s essential to allocate resources strategically, ensuring robust security measures without overspending.
Start by establishing a realistic budget that encompasses all aspects of your hosting needs, including DDoS protection. Consider both current requirements and future growth, as your needs may evolve over time. Allocating funds for potential upgrades, additional security measures, or increased resource demands will help you remain prepared for any eventualities.
When evaluating potential hosting providers, ensure that their offerings align with your budget. Compare various plans to identify options that provide robust DDoS protection without compromising essential features. This may involve balancing cost with performance, scalability, and support services.
Additionally, consider setting aside a contingency fund for unexpected incidents, such as a sudden traffic spike from a DDoS attack. Having a financial buffer will enable you to respond quickly to threats, ensuring that your website remains secure and operational, even during challenging circumstances.
In the journey of how to choose hosting with ddos protection, effective budget planning is essential. By conducting thorough assessments of your needs and strategically allocating resources, you can ensure that your hosting solution provides the necessary DDoS protection while remaining within financial constraints.
Evaluating Performance and Reliability in Hosting Solutions
Monitoring Server Response Time for Optimal Performance
Server response time is a critical metric for evaluating the performance of hosting providers, especially concerning DDoS protection. The speed at which a server responds to incoming requests directly impacts user experience and can be a determining factor in the overall effectiveness of your hosting solution during an attack.
A shorter server response time translates to reduced latency, allowing users to access your website more quickly, which is crucial for retaining visitors and achieving business objectives. During a DDoS attack, even a slight increase in response time can significantly affect user access, potentially leading to frustration and lost revenue. Therefore, choosing a hosting provider with optimized servers capable of maintaining low response times is essential.
To gauge server response times, consider conducting performance tests using tools that simulate real user interactions. These tests can provide valuable insights into how well a provider performs under both normal and heavy traffic conditions. Ensure that the hosting provider you choose has a proven track record of maintaining consistent response times, even during peak loads.
When exploring how to choose hosting with ddos protection, prioritize server response times as a crucial performance metric. By selecting a hosting provider known for speed and efficiency, you can enhance user experience and ensure that your website remains accessible, even under duress.
Understanding Uptime Guarantees in Hosting Contracts
Uptime guarantees are a vital component of hosting service agreements, reflecting a provider’s commitment to maintaining service availability. High uptime percentages indicate that a hosting provider effectively mitigates DDoS attacks and other potential disruptions, ensuring your website remains online and accessible to users.
Seek out hosting providers that offer uptime guarantees of 99.9% or higher, as this demonstrates their focus on reliability. A robust uptime guarantee often implies that the provider has implemented advanced infrastructure, including redundant systems and effective DDoS protection measures, to minimize downtime.
Moreover, it is crucial to understand the terms of these uptime guarantees. Some providers may specify conditions under which the guarantee applies, while others may provide compensation for service interruptions. Familiarizing yourself with the details of these agreements can help you gauge the true level of commitment a provider has to uptime and service continuity.
In your exploration of how to choose hosting with ddos protection, prioritize uptime guarantees as a critical consideration. By selecting a hosting provider that demonstrates a strong commitment to maintaining high levels of service availability, you can ensure that your online presence remains secure and accessible to your audience.
Utilizing Load Balancing for Enhanced DDoS Protection
Load balancing is an essential feature that significantly enhances the performance and reliability of hosting providers, particularly in the context of DDoS protection. By distributing incoming traffic evenly across multiple servers, load balancing helps minimize the impact of DDoS attacks, maintaining service availability even during periods of heavy traffic.
Efficient load balancing ensures that no single server becomes overwhelmed with requests. When a DDoS attack occurs, the load balancer can redirect traffic to servers with available resources, preventing service disruptions. This capability is crucial for organizations that experience fluctuating traffic levels, ensuring that legitimate users can access the site without interruption.
When selecting a hosting provider, inquire about their load balancing capabilities and how they integrate with their DDoS protection measures. Providers offering advanced load balancing solutions, including global server load balancing (GSLB), can further enhance resilience against attacks by directing traffic to the nearest or least-congested server.
As you consider how to choose hosting with ddos protection, prioritize load balancing as a critical factor. A hosting provider with robust load balancing features will help safeguard your online presence, ensuring that your website remains operational and accessible, even in the face of DDoS threats.
Exploring Comprehensive DDoS Protection Services
Selecting a hosting provider that offers comprehensive DDoS protection services is essential for safeguarding your website against malicious traffic. These services are designed to detect and mitigate a wide range of DDoS attacks, ensuring that your online assets remain secure and accessible.
DDoS protection services typically include a combination of traffic filtering, rate limiting, and automated mitigation strategies to counteract attacks effectively. A robust protection service will analyze incoming traffic patterns in real-time, identifying and blocking malicious requests while allowing legitimate traffic to flow through seamlessly.
Additionally, consider hosting providers that utilize cloud-based DDoS protection solutions. These services can absorb and neutralize large-scale attacks before they reach your servers, offering an additional layer of security. Cloud-based solutions are particularly effective during sophisticated attacks, ensuring that your website remains operational even in the face of overwhelming traffic.
When exploring how to choose hosting with ddos protection, prioritize providers that offer comprehensive DDoS protection services. By selecting a hosting solution with robust security features, you can ensure your website remains secure from DDoS threats, protecting both your business’s reputation and revenue.
Implementing Security Measures Beyond DDoS Protection
Integrating Firewalls for Comprehensive Online Security
Integrating firewalls with DDoS protection measures is a crucial aspect of a comprehensive security strategy. Firewalls serve as the first line of defense, blocking unauthorized access and filtering out potentially harmful traffic before it reaches your servers. This integration enhances overall security, ensuring that your online assets remain protected against a myriad of threats.
Modern firewalls extend beyond traditional packet filtering, incorporating advanced features such as intrusion detection and prevention systems (IDPS). These systems analyze traffic patterns in real time, identifying and responding to suspicious activities that may indicate an ongoing DDoS attack. By merging DDoS protection with firewalls, hosting providers can strengthen their defenses, ensuring a multi-layered approach to security.
In addition to blocking malicious traffic, firewalls also help manage legitimate traffic during high-demand periods. By establishing strict rules and policies, they can prevent server overload and ensure that available resources are allocated efficiently. This capability is particularly important during DDoS attacks, as it enables organizations to minimize disruptions while maintaining service availability.
As you consider how to choose hosting with ddos protection, prioritize providers that offer robust firewall integration as part of their security measures. A hosting solution that combines DDoS protection with advanced firewall capabilities will provide a strong defense against malicious activities, ensuring your online presence remains secure.
Implementing SSL/TLS Encryption for Enhanced Online Security
SSL/TLS encryption is a critical component of online security that protects sensitive data and plays a role in mitigating certain types of DDoS attacks. By encrypting data transmitted between users and servers, SSL/TLS encryption helps safeguard against eavesdropping and man-in-the-middle attacks, enhancing overall security.
Beyond its protective benefits, SSL/TLS encryption can also help reduce the impact of specific DDoS attacks. For instance, attackers may target unencrypted connections to exploit vulnerabilities or launch application layer attacks. By implementing SSL/TLS, organizations create a more secure environment that complicates attackers’ efforts to compromise their systems.
Moreover, enabling SSL/TLS encryption can improve user trust. Modern web browsers indicate secure connections by displaying padlock icons, signaling to users that their data is protected. This enhanced trust can lead to increased customer confidence and engagement, particularly for e-commerce sites or services that require sensitive information.
When exploring how to choose hosting with ddos protection, prioritize providers that offer SSL/TLS encryption as part of their security measures. By combining DDoS protection with encryption, you can create a more secure online environment for your users, safeguarding both your data and your reputation.
Conducting Regular Security Audits for Continuous Protection
Conducting regular security audits is essential for maintaining a robust defense against DDoS attacks and other cybersecurity threats. These audits serve to assess the effectiveness of existing security measures, identify vulnerabilities, and ensure that your hosting environment remains secure.
During a security audit, various aspects of the hosting infrastructure are examined, including firewall configurations, server settings, and DDoS protection mechanisms. This comprehensive evaluation helps identify weaknesses that could be exploited by attackers, allowing organizations to proactively enhance their defenses.
Furthermore, regular security audits can help organizations remain compliant with industry standards and regulations. Compliance is essential for businesses handling sensitive data, as it demonstrates a commitment to maintaining high security standards. Regular audits can also foster a culture of security awareness within the organization, encouraging employees to adopt best practices.
When considering how to choose hosting with ddos protection, prioritize providers that emphasize regular security audits as part of their service offerings. A hosting provider committed to ongoing security assessments will not only help safeguard your assets against DDoS attacks but also ensure your organization remains vigilant against evolving threats.
Frequently Asked Questions (FAQs)
What is the definition of a DDoS attack?
A DDoS attack is a malicious attempt to disrupt the normal functioning of a targeted server or network by overwhelming it with excessive traffic, leading to service outages that hinder user accessibility.
How can I effectively protect my website from DDoS attacks?
To safeguard your website, choose a hosting provider that offers robust DDoS protection features, including traffic filtering, real-time monitoring, and automated mitigation solutions tailored to counteract potential threats.
What are the main categories of DDoS attacks?
The primary categories of DDoS attacks include volumetric attacks that inundate bandwidth, protocol attacks that exploit weaknesses in network protocols, and application layer attacks that specifically target web applications or services.
Why is uptime paramount in hosting services?
Uptime is critical as it reflects a hosting provider’s reliability. High uptime guarantees ensure that your website remains accessible to users, even during DDoS attacks or other disruptions.
What should I focus on in a hosting provider’s SLA?
Focus on uptime guarantees, response time commitments, and clear terms regarding the provider’s response to DDoS attacks and compensation measures in the event of service disruptions.
How does load balancing assist during DDoS attacks?
Load balancing distributes incoming traffic across multiple servers, preventing any single server from becoming overwhelmed during a DDoS attack, thus maintaining service availability for legitimate users.
What advantages does SSL/TLS encryption provide?
SSL/TLS encryption secures data transfers between users and servers, enhances user trust by indicating secure connections, and helps mitigate certain types of DDoS attacks by safeguarding against vulnerabilities.
Why is customer support crucial for hosting providers?
Reliable customer support is essential during a DDoS attack, as access to knowledgeable support staff can facilitate rapid issue resolution, allowing for prompt mitigation and minimizing service disruptions.
How frequently should I conduct security audits?
Regular security audits should be performed at least annually or more frequently if your website undergoes significant changes or as new threats emerge, ensuring ongoing protection against vulnerabilities.
What factors influence the cost of DDoS protection services?
The cost of DDoS protection can be influenced by factors such as the hosting provider’s pricing model, the level of protection offered, and any additional features or services included in the plan.
Follow our journey on X!
The Article How to Choose Hosting with DDoS Protection: Essential Tips was first published on https://marketing-tutor.com
The Article Choosing Hosting with DDoS Protection: Key Tips to Consider Was Found On https://limitsofstrategy.com
-

Security System Wiring Solutions for Smart and Safe Compliance
The Critical Importance of Expert Electrical Wiring for Home Security Systems
Hiring a professional for your security system installation is not just a recommendation; it’s a necessity. Any system functioning on 240V power, such as CCTV systems, hardwired alarms, and video intercoms, must be handled by a qualified electrician. In Victoria, installations must adhere to the AS/NZS 3000 standards, ensuring that they have essential circuit protection, proper cable segregation, and IP-rated enclosures to withstand outdoor conditions. This compliance is vital not only for the effective operation of your home security system but also for prioritizing safety and ensuring adherence to local regulations.

Key Components and Compliance Standards of Modern Security Systems
Today’s security systems encompass a wide array of components that extend far beyond just conventional surveillance cameras. They now feature advanced sensors, alarms, intercoms, electric locks, and cloud-based hubs. Each of these elements requires reliable and compliant electrical work to ensure optimal functionality. Homeowners in areas like Narre Warren North, Berwick, Devon Meadows, and Clyde are increasingly investing in these innovative security solutions, seeking not only enhanced safety but also the invaluable peace of mind that comes with comprehensive protection.
At Direct Point Electrical, we excel in the meticulous wiring of smart security systems that are designed to function quietly, efficiently, and in full compliance with legal frameworks. Our dedication includes ensuring that all installations meet rigorous standards, certified by a Certificate of Electrical Safety (COES), providing our clients with confidence in the efficiency and reliability of their home security systems.
Understanding the Comprehensive Scope of Security Wiring
<pWhen we talk about security system wiring, we are referring to all fixed, powered components that integrate into your surveillance, alarm, or entry system. This includes a wide variety of devices such as:
- CCTV systems that utilize Power over Ethernet or DC-powered options for efficient operation
- Wired alarm panels and PIR sensors crucial for detecting motion
- Doorbell intercoms that facilitate clear communication
- Electronic deadbolts or strikes enhancing secure access
- External motion lights equipped with integrated cameras for added surveillance
- Garage entry systems designed for secure vehicle access
- Gate controllers or swipe access systems for heightened security
Whether you are installing a DIY kit or a professional-grade NVR, if your setup connects to the 230V supply or involves fixed cabling, it is absolutely essential to enlist the services of a licensed electrician to ensure safety and compliance with all relevant standards.
Discover Our Comprehensive Wiring Services and Their Significance
1. Reliable Hardwired CCTV Systems for Enhanced Security
Hardwired CCTV cameras provide a level of reliability that far surpasses their Wi-Fi counterparts, making them especially suitable for:
- Larger homes that require extensive surveillance coverage
- Long retention storage capabilities through a NVR for video footage
- External monitoring capabilities to enhance security measures
- Smart motion alerts that provide immediate notifications for any activity
We offer a comprehensive range of services, which includes:
- Routing low voltage DC power to ensure optimal performance
- Installing conduits to protect wiring on exterior runs against environmental factors
- Setting up Power-over-Ethernet switches for seamless connectivity
- Implementing surge protection to safeguard outdoor lines from electrical surges
Learn more about our offerings on our Security System Wiring page.

2. Advanced Wired Alarm Panels for Optimal Security Management
Many modern security systems incorporate fixed PIR sensors, panic buttons, and siren alarms that are connected to a central control panel for effective monitoring and management.
Our installation services encompass:
- Running 12V or 24V DC power cabling directly from the switchboard
- Utilizing separate conduits or cable trays for maintaining power and signal integrity
- Installing isolation switches and battery backups to enhance reliability
- Providing mounting, programming, and testing support to ensure seamless operation
3. High-Performance Video Doorbells and Intercom Systems for Enhanced Communication
While popular brands like Ring, Arlo, and Hikvision offer convenient Wi-Fi versions, wired intercoms provide:
- Superior video/audio quality for clearer communication
- A secure power supply that guarantees consistent operation
- Integration capabilities with electric gates or locks for enhanced security
We provide a full range of services, including:
- Installation of low-voltage transformers for reliable power supply
- Running external conduits for front gate wiring while maintaining aesthetic appeal
- Providing IP-rated enclosures for outdoor stations to withstand various weather elements
- Cabling through brickwork or render to ensure minimal damage during installation
4. Effortless Wiring Solutions for Electronic Locks and Garage Access Systems
We ensure safe and reliable wiring for a variety of access systems, including:
- Strike plates that facilitate secure entry
- Keypad locks that enhance the security of your premises
- Swipe card or fob access systems that provide modern conveniences
- Smart garage door controllers that can be wired or relay-based for flexibility
While many of these systems operate at low voltage, they must be wired to a secure, isolated DC power supply, avoiding shared points or multi-use plugs to maintain safety and optimal functionality.
Determining the Necessity of a Dedicated Circuit for Your Security Installation
In numerous situations, the answer is yes. If you are incorporating:
- Multiple cameras to ensure comprehensive coverage
- High-powered NVRs for effective video storage
- Integrated lighting systems to improve visibility
- Wireless hubs or control units for smart management
Then a dedicated 10A–16A circuit may be required to prevent overloads and ensure proper separation from other household electrical loads, thereby enhancing safety.
We can also combine this circuit upgrade with a Switchboard Upgrade if your current board is full, outdated, or lacks RCDs for added safety and compliance.
Integrating Innovative Smart Technology into Your Security System
We craft comprehensive wiring layouts that facilitate:
- Google Home / Alexa control of alarms for user convenience
- IFTTT automation (e.g., “If door opens, turn on porch light” for smart functionality)
- Push notifications sent directly to your mobile devices for immediate alerts
- Remote lock/unlock capabilities for added convenience
Many smart systems still necessitate fixed wiring at key locations (such as chimes, transformers, or PoE switches), which must be installed by a licensed professional to ensure seamless operation and compliance with safety standards.
Discover more about our innovative solutions in our Smart Home Wiring section.

Frequently Asked Questions About Security Wiring Solutions
Can I install my own wired security system?
No, it is not advisable to undertake this task if it connects to mains power or involves fixed cabling. DIY installations are generally limited to plug-and-play wireless kits that do not require extensive electrical work, ensuring safety and compliance with regulations.
Are wireless systems exempt from needing an electrician?
While the initial setup might not require professional assistance, if you plan to power them using wall-mounted transformers or need to hardwire lights or alarms, you will indeed require an electrician for safe installation.
Is a permit necessary to wire a CCTV system?
No permit is needed; however, all electrical work must be executed by a licensed electrician, and it must comply with state regulations to ensure safety and legality.
What is the average time required for security wiring installation?
Most full-system installations, which typically include CCTV, intercoms, and sensors, usually take between 1 to 2 days. The duration may vary based on the layout of the home and accessibility to the installation areas, ensuring thorough and quality work.
Is surge protection a necessity for security systems?
Yes, surge protection is essential for all outdoor components and PoE lines. We install surge arresters to protect your system from issues like lightning strikes or electrical faults from the grid, ensuring long-term reliability and functionality.
Enhance Your Security with Premium Wiring Solutions
Robust security begins with dependable wiring solutions. Whether you are monitoring your driveway with cameras, connecting sensors to a smart lock, or securing your garage, the system will only function effectively if the underlying electrical infrastructure is solid and reliable.
Direct Point Electrical is committed to delivering fully certified, standards-compliant security system wiring throughout Melbourne’s outer east. We focus on safety, efficiency, and peace of mind, ensuring that your security measures are both effective and dependable.
The Article: Security System Wiring: Compliant, Smart, and Safe Solutions first appeared on https://writebuff.com
The Article Security System Wiring Solutions: Smart, Safe, and Compliant Was Found On https://limitsofstrategy.com
-
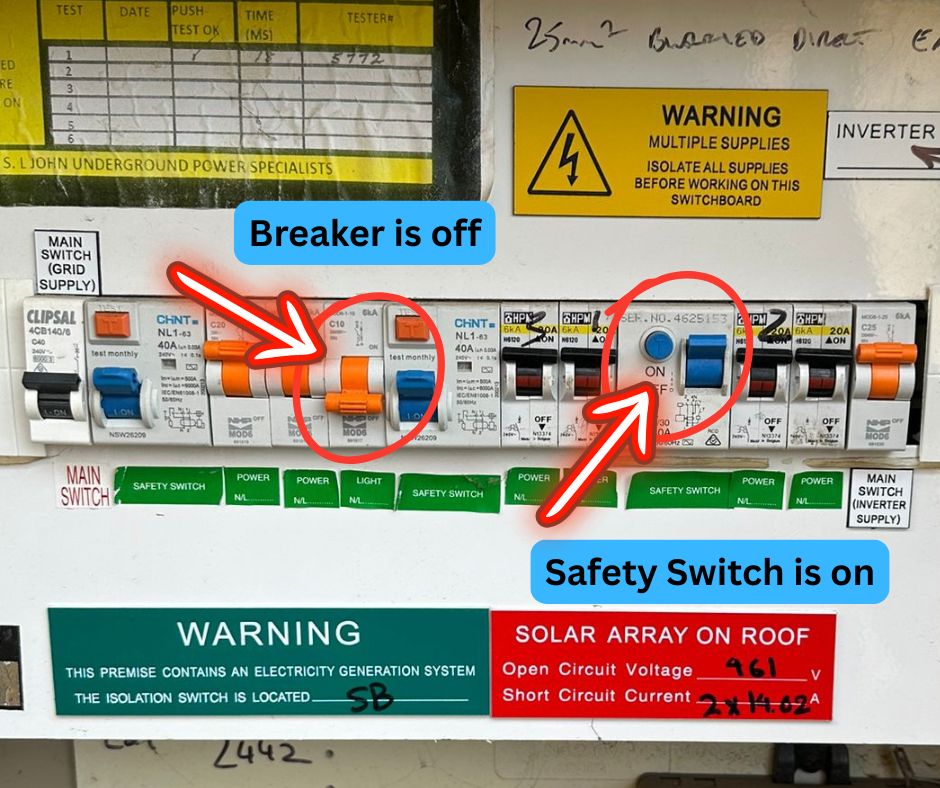
Switchboard Upgrade Warning Signs: Is Your Home Secure?
Identifying the Key Warning Signs That Indicate Your Switchboard Needs Immediate Upgrade
Frequent occurrences of tripped circuit breakers, flickering lights, alarming burning odours, outdated fuses, and the lack of safety switches are significant red flags that suggest your switchboard may not meet safety standards or be compliant with current Australian Standards (AS/NZS 3000). These serious issues can lead to dire risks, including electric shock, damage to appliances, or even severe fire hazards. It is crucial to have a qualified electrician assess your electrical system promptly to ensure your safety and adherence to existing regulations, thereby protecting your home and loved ones from potential dangers.
Understanding the Vital Function of Switchboards in Your Home’s Electrical Framework
The switchboard in your residence plays an essential role, acting as the central hub of your electrical system. If it is outdated or showing signs of malfunction, it could greatly compromise your safety and well-being. Many older homes, particularly in Melbourne’s outer southeast, are still relying on electrical systems established decades ago, long before the implementation of modern electrical safety standards. Upgrading your switchboard is not merely a matter of routine upkeep; it is a crucial measure to ensure that your home adheres to current regulations and minimizes any potential safety hazards associated with obsolete installations, thus safeguarding your family and property.
In this article, we will comprehensively explore the primary warning signs that suggest your switchboard may require replacement, highlighting the significance of regulatory compliance and the dangers associated with ignoring these critical indicators that could affect your home’s safety.
1. Frequent Circuit Breaker Trips Reveal Potential Overload Issues
Noticing that your circuit breakers are tripping often, particularly when multiple appliances are in use, may indicate your switchboard is facing overload problems. These frequent interruptions can signal poor load distribution, inadequate wiring, or aging breakers that are no longer functioning safely. Regularly tripping circuit breakers can disrupt your routine and may lead to more severe electrical issues if not addressed promptly. For further insights on enhancing the reliability of your electrical system, consider exploring our Electrical Panel Upgrade Services tailored to improve your system’s efficiency and safety.
2. Flickering or Dimming Lights Indicate Voltage Instability Issues
If you observe your lights flickering or dimming, especially when appliances start up, it often signals issues related to voltage fluctuations. This problem typically arises from loose or deteriorated connections within the switchboard or a system that struggles to manage load surges effectively. Such electrical instability can lead to further complications, including damage to sensitive electronic devices and appliances. It is vital to address this issue swiftly to maintain a stable and safe electrical environment throughout your home, ensuring that your devices function optimally without interruptions.
3. Detecting Burning Smells or Heat Marks Signifies a Critical Hazard
If you detect a burning odour near your switchboard or see visible signs of charring, discoloration, or melted plastic, these are alarming signs that should not be ignored. These indicators typically signify overheating or arcing occurring inside the switchboard, both of which significantly elevate the risk of fire. If you encounter any of these concerning signs, it is essential to take immediate action to protect your home and loved ones from potential hazards. For further information on electrical fire risks, please visit the Victorian Building Authority, which provides valuable resources on electrical safety and regulations.
4. Presence of Outdated Ceramic Fuses Signals the Need for Modern Electrical Safety Features
Finding ceramic fuses in your switchboard, particularly those installed before the 1990s, indicates that your electrical system may be outdated and in need of urgent attention. Unlike modern circuit breakers, ceramic fuses lack rapid-response safety features and do not provide adequate protection against electric shock. Current wiring standards, specifically AS/NZS 3000:2018, mandate that all final sub-circuits must be equipped with a safety switch (RCD) for enhanced protection. If your switchboard still contains ceramic fuses, it is not only outdated but also poses potential dangers that should be addressed without delay to ensure the safety of your electrical system.
5. Warm or Hot Switchboard Panels Indicate Overloaded Circuits
Your switchboard should generally maintain a temperature that aligns with room temperature during regular operation. If you find that its surface is warm or hot to the touch, this usually indicates poor internal connections or overloaded circuits. Continuous exposure to excessive heat can lead to the degradation of insulation or even result in permanent damage to the internal wiring. Investigating and resolving this issue is crucial to prevent further complications and ensure the safety and efficiency of your home’s electrical system, thereby avoiding dangerous situations that could affect your household.
6. Outdated Switchboards Struggle to Meet Contemporary Appliance Demands
As the prevalence of high-demand electrical devices in modern homes continues to increase, including larger air conditioning systems, induction cooktops, electric vehicles, and extensive home office setups, older switchboards often find themselves unable to safely accommodate these increasing loads. Many of these outdated switchboards were not designed with current demands in mind, rendering them susceptible to hazardous overload situations. Upgrading to a modern switchboard is essential to ensure that your home’s electrical system can effectively and safely support all your energy needs, providing peace of mind that your electrical infrastructure is up to the task.
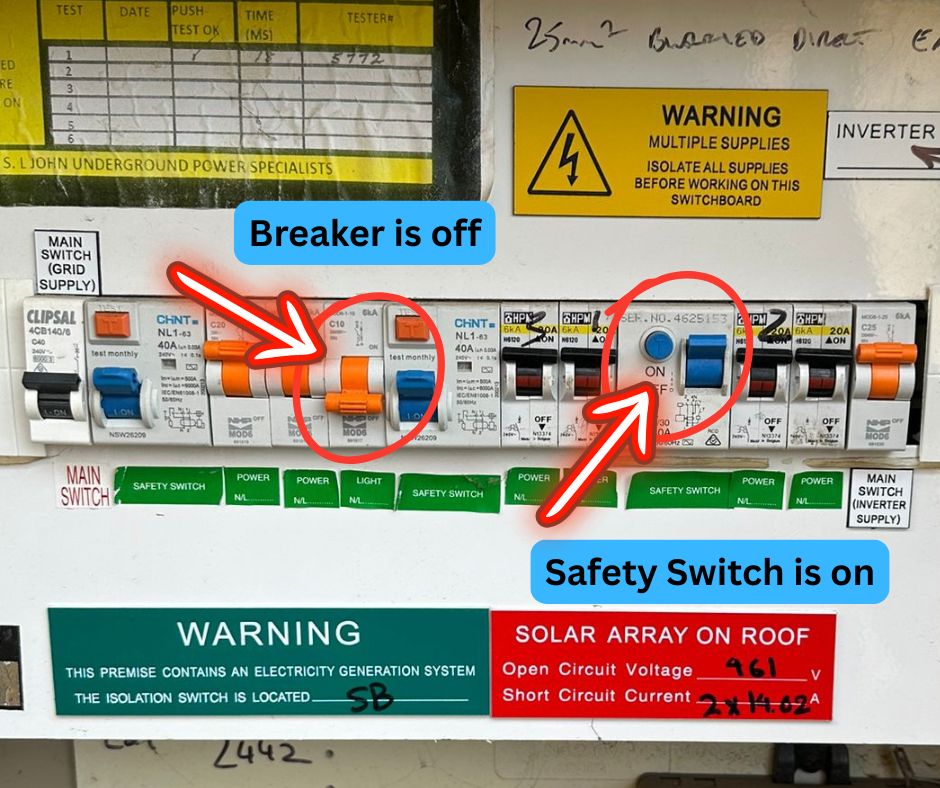
7. Absence of Safety Switches (RCDs) Represents a Major Compliance Concern
In the absence of safety switches (RCDs) in your switchboard, your property fails to comply with essential modern protection standards. RCDs are now required for all new installations and electrical work, as mandated by AS/NZS 3000. Moreover, recent changes to rental property laws enforced by Energy Safe Victoria since March 29, 2023, require that all rental homes in Victoria be equipped with compliant circuit breakers and RCDs. It is crucial to review and adhere to these updated standards to ensure the safety of your property and its occupants, protecting them from potential electrical hazards.
8. Potential Asbestos Exposure in Older Switchboards Poses Serious Health Risks
Older switchboards, particularly those installed prior to 1985, may contain asbestos within their backing panels or internal components, posing significant health risks. Exposure to asbestos can lead to severe respiratory complications and other serious health issues. The legal removal of asbestos must be conducted by licensed professionals trained in safe asbestos handling. Therefore, it is advisable to schedule a comprehensive Home Electrical Inspection with a qualified electrician before attempting any alterations or removals of older switchboard housings to mitigate health risks associated with asbestos exposure.
9. Unusual Noises from Your Switchboard Indicate Serious Electrical Issues
If you hear unusual sounds such as buzzing, popping, or cracking coming from your switchboard, or if you notice breakers with scorch marks or melted plastic, these are clear indicators of internal arcing or overload. Such issues require immediate attention to prevent the risk of fire or damage to your appliances. Taking prompt action is essential to maintain the safety and functionality of your electrical system, ensuring that your home remains a safe environment for you and your family.
10. Legal and Insurance Risks Linked to Non-Compliant Switchboards
An outdated or non-compliant switchboard can jeopardize your insurance coverage in the unfortunate event of an electrical fire. Compliance with Australian Standards is required by both federal and state authorities. Any property undergoing renovations, appliance upgrades, or tenancy changes must adhere to the latest safety requirements to avoid legal repercussions and ensure the well-being of all occupants while protecting against potential liabilities associated with electrical hazards.
Why Choose Direct Point Electrical for Your Switchboard Upgrade?
Located in outer east Melbourne, Direct Point Electrical specializes in switchboard upgrades that ensure compliance with current safety standards while significantly enhancing your home’s overall safety. Our team of experienced electricians is dedicated to upgrading legacy homes, ensuring adherence to:
- AS/NZS 3000:2018 Wiring Rules
- Energy Safe Victoria requirements
- All local DNSP and safety notice obligations
- Certification through Certificate of Electrical Safety (COES)
Our comprehensive Switchboard Upgrade Services include evaluation, safe removal of asbestos, installation of RCDs, and optional surge protection to enhance the safety and efficiency of your home’s electrical system, ensuring that you are well-equipped for today’s electrical demands.
Frequently Asked Questions About Switchboard Upgrades
Q: How often should I have my switchboard inspected?
A: It is advisable to have your switchboard inspected every five years or whenever you introduce significant electrical loads into your home to ensure ongoing safety and compliance with current standards.Q: Is it possible for me to perform a switchboard upgrade myself?
A: No, switchboard upgrades must only be carried out by a licensed electrician to ensure safety and compliance with all current regulations, protecting both you and your property.Q: What is the typical duration for a switchboard upgrade?
A: Most upgrades can be completed within a single day, minimizing disruptions to your household activities while ensuring that safety measures are implemented swiftly and effectively.Q: Will upgrading my switchboard increase my home’s market value?
A: Absolutely, an upgraded electrical system is highly attractive to potential buyers and can significantly enhance your property’s value in a competitive real estate market.The Article: Switchboard Upgrade Warning Signs: Is Your Home Safe? first appeared on https://writebuff.com
The Article Warning Signs of a Switchboard Upgrade: Is Your Home Safe? Was Found On https://limitsofstrategy.com
-

Blood Test Privacy: Ensuring Compliance and Data Safety
Comprehensive Guide to Navigating UK Data Protection Laws for Healthcare Providers and Patients
Understanding the intricate landscape of data privacy in the United Kingdom necessitates a deep dive into the extensive legislative frameworks designed to protect personal information. This understanding becomes even more critical when addressing sensitive data related to blood test privacy concerns. It is vital for both patients and healthcare providers to develop a robust awareness of these regulations, as this knowledge is key to ensuring the effective safeguarding of personal health information. By embracing these laws, both parties can manage health data with the highest degree of integrity, ultimately cultivating trust in healthcare practices and systems.
Exploring the Impact of GDPR on Health Data Management in the UK

The implementation of the General Data Protection Regulation (GDPR) has significantly transformed the management of personal data, particularly health-related data, in the UK since its introduction in 2018. GDPR sets forth rigorous standards regarding the collection, processing, and storage of personal data, compelling organizations to uphold transparency and accountability in their data handling practices. For patients, this means they receive clear communication regarding how their blood test information will be utilized, ensuring that informed consent is obtained prior to any data processing actions.
Under GDPR, patients are granted the right to access their health data and inquire about any third parties that may have access to this information. This regulation places specific responsibilities on healthcare providers, obligating them to implement appropriate technical and organizational measures to protect personal data from potential breaches. Non-compliance with GDPR can result in substantial financial penalties, rendering adherence to these regulations a critical priority for healthcare institutions across the UK.
As a result, GDPR not only enhances patient privacy but also empowers individuals to take control of their personal health information. Patients are now better equipped to seek clarity regarding their blood test privacy concerns, with the expectation that their data will be treated with the utmost security and respect.
Key Elements of the Data Protection Act 2018 Explained
The Data Protection Act 2018 serves as an essential complement to GDPR, establishing the foundational legislation for data protection in the UK, particularly concerning health data. This act outlines specific protocols for processing health data, providing enhanced protections for sensitive categories of information, such as genetic and biometric data associated with blood tests.
A fundamental principle of this legislation is the emphasis on data minimisation. Healthcare providers are encouraged to collect only the necessary data essential for clearly defined purposes, thereby reducing the risks of unnecessary exposure and breaches. Additionally, the Act safeguards the rights of patients, granting them greater control over their health data, including the ability to correct inaccuracies and request the deletion of their data under specific circumstances.
The Data Protection Act 2018 is crucial in promoting a culture of compliance and respect for patient privacy within the UK healthcare system. It highlights the importance of ethical data handling practices, ensuring that blood test privacy concerns are prioritized and effectively addressed by all stakeholders involved in delivering healthcare services.
Empowering Patients with Rights Under UK Data Protection Framework
In the UK, patients are endowed with a wide range of rights under data protection laws, granting them substantial control over their personal health information. These rights, enshrined within both GDPR and the Data Protection Act 2018, encompass the right to access their blood test data, rectify inaccuracies, and request the deletion of their data at their discretion.
The right to access personal data is fundamental, enabling patients to understand what information is held about them and how it is utilized. This transparency is vital in building trust between patients and healthcare providers, which is essential for the delivery of effective care. Additionally, if a patient notices discrepancies in their blood test results, they have the right to request corrections, ensuring that their medical records accurately reflect their health status and history.
Moreover, patients can exercise their right to erasure, commonly known as the right to be forgotten, which allows them to request the deletion of their personal data under specific circumstances, such as when the data is no longer necessary for the purposes for which it was collected. This right not only empowers patients but also compels healthcare providers to maintain accurate and relevant data, thereby alleviating blood test privacy concerns.
The framework of patient rights established under UK law exemplifies the country’s commitment to protecting individual privacy and fostering a more respectful healthcare environment for all patients.
Evaluating the Risks Associated with Data Breaches in Healthcare Environments

In an increasingly digital world, the risks linked to data breaches within healthcare settings are on the rise. Such breaches can have serious repercussions for patients, especially concerning their sensitive health information, encompassing blood test privacy concerns.
Recognizing Different Types of Data Breaches in Healthcare
Healthcare institutions in the UK face various types of data breaches that threaten patient information. One common form of breach is hacking, where cybercriminals infiltrate systems to access and extract sensitive data. The National Cyber Security Centre (NCSC) has reported a troubling increase in cyberattacks targeting healthcare providers, particularly during crises like the COVID-19 pandemic, when data security measures may be compromised.
Another significant threat arises from insider risks, where employees within healthcare organizations unintentionally or maliciously compromise patient data. This can happen through negligence, such as failing to secure login credentials or accessing data unrelated to their job responsibilities, or through more deliberate actions, including selling data on the dark web.
Physical theft of records also remains a considerable risk, with sensitive documents being left unsecured or lost, leading to potential blood test privacy concerns for patients whose information is compromised.
The variety of these breaches underscores the urgent need for stringent data protection measures within UK healthcare settings to mitigate risks and ensure the effective safeguarding of patient data.
Understanding the Consequences of Data Breaches for Patients
The ramifications of data breaches extend far beyond the immediate loss of data; they can fundamentally disrupt patients’ lives. Identity theft is among the most concerning outcomes, where stolen information is used to impersonate the victim, often resulting in financial loss and emotional distress. For patients whose blood test data is compromised, the fallout can be particularly damaging, as others may gain access to sensitive health information that could be exploited.
Moreover, breaches can facilitate medical fraud, where individuals misuse health data to acquire services or medications under false pretenses. Such fraudulent actions not only harm the victims but can also distort healthcare statistics and lead to increased insurance premiums for everyone.
Another critical consequence of data breaches is the erosion of trust in healthcare providers. Patients may hesitate to share critical health information, fearing that their data will not be adequately protected. This apprehension can hinder accurate diagnosis and treatment, ultimately jeopardizing patient care and public health outcomes.
The multifaceted repercussions of data breaches highlight the pressing need for robust data protection measures and heightened awareness regarding blood test privacy concerns.
Implementing Effective Preventive Strategies in UK Hospitals

In response to the escalating threat of data breaches, UK hospitals are adopting a variety of preventive measures specifically designed to protect patient data, particularly sensitive blood test information. One of the most effective strategies is the implementation of encryption, which protects data by converting it into a coded format that is accessible only to authorized personnel. This ensures that even if data is intercepted, it remains unreadable to unauthorized individuals.
Access controls are another critical preventive measure, limiting the number of personnel who can access sensitive patient data. By employing role-based access, hospitals can ensure that only those who genuinely need access to blood test results have the authority to view them. This significantly reduces the risk of insider threats and mitigates potential accidental data exposure.
Additionally, regular audits are conducted to assess the effectiveness of data protection protocols and identify vulnerabilities. These audits assist institutions in staying ahead of potential threats while ensuring compliance with UK data protection laws.
Training staff on data protection best practices is also essential. Healthcare providers must adequately inform their employees about the importance of safeguarding personal information and the procedures in place to ensure its security. This comprehensive approach to data security not only aids in preventing data breaches but also promotes a culture of safety and respect for patient privacy within healthcare organizations.
Through the implementation of these preventive measures, UK hospitals are making significant progress in addressing blood test privacy concerns and ensuring the security of patient data.
Examining the Legal and Regulatory Consequences of Data Breaches
The legal framework governing data breaches in UK healthcare is stringent, with substantial penalties for non-compliance with data protection regulations. Under GDPR, organizations may face fines of up to £17.5 million or 4% of their annual global turnover, whichever figure is higher. Such significant penalties serve as a powerful deterrent against negligence in data handling.
In addition to financial repercussions, organizations may also encounter legal actions from affected individuals. Patients whose data has been compromised can seek damages, further incentivizing healthcare providers to uphold rigorous data protection measures. The reputational damage resulting from a breach can be equally detrimental, as trust erodes and patients may choose to seek care elsewhere.
Moreover, data breaches can trigger investigations by regulatory authorities. The Information Commissioner’s Office (ICO) is tasked with ensuring compliance with data protection laws in the UK, and any breaches may prompt thorough inquiries and increased scrutiny. This regulatory oversight not only enforces accountability but also fosters a culture of compliance within healthcare institutions.
The legal and regulatory ramifications of data breaches underscore the critical need for healthcare providers to prioritize blood test privacy concerns and implement comprehensive data protection strategies to effectively safeguard patient information.
Clarifying Consent in Blood Test Data Management
The intersection of patient autonomy and data protection is encapsulated in the fundamental issue of consent concerning blood test privacy concerns. In the UK, consent is more than a mere formality; it is a foundational principle that underpins the ethical management of personal health information.
Ensuring Comprehensive Informed Consent for Patients
Informed consent is crucial in ensuring that patients are fully aware of how their blood test data will be utilized and stored. Healthcare providers in the UK are required to provide clear and comprehensive information regarding the purposes of data collection, the processing involved, and the potential risks associated with data handling.
Patients must be made aware of who will have access to their data, whether it will be shared with third parties, and the duration for which it will be retained. This not only empowers patients but also aligns with the principles of transparency and accountability mandated by UK data protection laws.
The process of obtaining informed consent should also emphasize that patients have the right to ask questions and seek clarifications. This empowerment enables individuals to make informed decisions regarding their health data, thereby fostering trust between patients and healthcare providers.
Furthermore, consent must be obtained prior to any processing activities, ensuring that patients are not caught off guard by how their personal information is used. This proactive approach to consent is vital for addressing blood test privacy concerns and reinforcing the significance of patient rights within the healthcare system.
Upholding Patients’ Right to Withdraw Consent
A significant aspect of UK data protection law is that patients retain the right to withdraw their consent for the use of their blood test data at any time. This right serves as a powerful mechanism for patients, allowing them to reclaim control over their personal information.
When patients choose to withdraw their consent, healthcare providers are obligated to cease any processing of their data and ensure that it is deleted or anonymised, adhering to the principles of data erasure. This right not only reinforces patient autonomy but also fosters a culture of respect for individual privacy within healthcare settings.
It is essential that healthcare providers actively communicate this right to patients, ensuring they understand that consent is not an indefinite agreement. Regular reminders about the ability to withdraw consent can empower patients and encourage open dialogue regarding their data privacy.
Moreover, facilities must establish clear procedures to efficiently manage consent withdrawals, ensuring that patient data is handled according to their preferences without unnecessary delay. This responsiveness is critical for alleviating blood test privacy concerns, demonstrating a commitment to respecting patient rights.
Special Considerations for Securing Consent from Minors Regarding Blood Tests
When seeking consent for blood tests involving minors, additional considerations arise. In the UK, the age of consent for data processing is typically set at 13 years, meaning that younger individuals require parental or guardian consent for their data to be processed lawfully.
Healthcare providers must ensure that parents or guardians are fully informed about the implications of data collection and processing, thereby securing the necessary consent on behalf of the minor. Additionally, it is crucial to respect the views and wishes of the child, depending on their maturity level and understanding of what consent entails.
For minors, special protocols are in place to safeguard their data, ensuring that sensitive health information, including blood test data, is managed with heightened care. This involves ensuring that consent forms are articulated in language that is accessible to both parents and children, facilitating their understanding of the potential uses of their data.
Furthermore, the right of the minor to withdraw consent should also be effectively communicated, allowing them to exercise their autonomy as they mature. By implementing tailored approaches for minors, healthcare providers can address blood test privacy concerns while promoting a culture of informed consent and respect for patient privacy.
Enhancing Data Protection with Anonymisation Techniques
The anonymisation of blood test data constitutes a vital component of data protection, particularly within a healthcare context where privacy concerns are paramount. UK regulations mandate that personal data must be anonymised wherever feasible to ensure the confidentiality of patient information.
Anonymisation refers to the process of removing identifiable information from datasets, rendering it impossible to link the data back to individual patients. This process is particularly significant in research contexts, where the use of anonymised data can yield valuable insights into health trends without jeopardizing individual privacy.
Healthcare institutions must adopt robust anonymisation techniques to protect patient identities, especially when sharing data with third parties for research or other purposes. The application of statistical methods and algorithms can significantly enhance the effectiveness of anonymisation, minimizing the risk of re-identification.
By prioritizing data protection and anonymisation, healthcare providers can effectively address blood test privacy concerns while simultaneously contributing to essential medical research and advancements. This delicate balance between patient privacy and the necessity for data in healthcare innovation is crucial for fostering a responsible and ethically sound healthcare environment.
The NHS’s Essential Role in Upholding Standards for Data Privacy
The National Health Service (NHS) plays a crucial role in establishing data privacy standards in the UK, particularly concerning blood test privacy concerns. With millions of patient records to manage, the NHS is at the forefront of implementing comprehensive data protection policies that safeguard patient information.
Understanding NHS Data Sharing Policies and Practices
The NHS has developed stringent data sharing policies that govern how patient information, including blood test data, is shared across various healthcare environments. These policies aim to balance the need for utilizing data for essential research and public health initiatives while simultaneously protecting patient privacy.
According to NHS guidelines, patient consent is generally required for data sharing, particularly when the information is used for secondary purposes, such as research or analysis. This ensures that patients maintain control over their data and are fully informed about its intended use.
Furthermore, the NHS promotes transparency in data sharing, encouraging healthcare providers to communicate clearly with patients about who has access to their information. This emphasis on openness not only builds trust but also reinforces the importance of ethical data handling within the healthcare system.
By adhering to these data sharing policies, the NHS is making significant strides in addressing blood test privacy concerns, ensuring that patient data is treated responsibly and ethically throughout the healthcare continuum.
NHS Digital’s Role in Strengthening Data Security Measures
NHS Digital plays an integral role in enhancing data security protocols for patient records across the UK. The organisation is responsible for managing digital health services and ensuring that data protection measures are effectively implemented.
One of NHS Digital’s primary objectives is to fortify the security of electronic health records (EHRs), which have become increasingly critical in modern healthcare. By deploying advanced security measures, including encryption and access controls, NHS Digital aims to mitigate risks associated with data breaches and unauthorized access to blood test data.
In addition to technological advancements, NHS Digital provides guidance and resources to healthcare providers, promoting best practices for data protection. Regular training sessions and awareness campaigns ensure that healthcare professionals understand the importance of safeguarding patient information and the measures in place to protect it.
The proactive approach adopted by NHS Digital not only addresses blood test privacy concerns but also fosters a culture of accountability and responsibility within the NHS, ensuring that patient data is managed with the utmost care and diligence.
Empowering Patients with Control Over Their NHS Data
Patients in the UK possess significant control over their NHS data, a vital aspect of addressing blood test privacy concerns. The NHS allows patients to opt out of specific data uses, enabling them to determine how their information is shared and for what purposes.
Patients can opt out of data sharing for particular purposes, such as research, ensuring that their personal health information remains confidential. This ability to control their data empowers patients and reinforces their rights under UK data protection laws.
Moreover, the NHS has developed an accessible platform for patients to manage their data preferences. This transparency enables individuals to make informed choices regarding their health information and promotes active engagement in their healthcare journey.
By providing patients with control over their data, the NHS is making significant progress in addressing blood test privacy concerns and ensuring that patient preferences are respected in all areas of healthcare delivery.
Safeguarding Blood Test Privacy in the Private Healthcare Sector
The private healthcare sector in the UK is also subject to rigorous data protection regulations, ensuring that blood test privacy concerns are adequately addressed in this context. Private clinics and laboratories must comply with the same legal frameworks as public institutions, diligently protecting patient information.
Data Management Practices in Private Clinics
Private clinics in the UK are required to handle patient data, including blood test data, in accordance with established data protection laws. This involves implementing robust security measures to safeguard sensitive information from breaches and ensuring that patient consent is obtained before any data processing occurs.
Similar to their public counterparts, private clinics must maintain transparency regarding how patient data is collected, used, and shared. This includes informing patients about the specific purposes of data collection and any potential third-party access to their information.
Furthermore, many private clinics are adopting best practices from the public sector, including regular audits and staff training on data protection. These initiatives are essential in cultivating a culture of respect for patient privacy and ensuring that data handling standards are consistently upheld.
By adhering to these stringent data handling practices, private clinics can effectively address blood test privacy concerns and build trust with their patients, reassuring them that their sensitive information is in safe hands.
Understanding Protocols for Sharing Blood Test Data with Third Parties
In the private healthcare sector, sharing blood test data with third parties is commonplace, especially for diagnostic testing and research purposes. However, such data sharing is contingent upon obtaining explicit patient consent, a principle that is fundamental to UK data protection regulations.
Patients must be informed about any potential data sharing arrangements and the specific purposes for which their data will be used. This transparency empowers patients to make informed decisions regarding whether to consent to the sharing of their health information.
Moreover, private entities must ensure that any third parties with whom they share data also comply with data protection regulations, thereby safeguarding patient information throughout the data chain. This includes conducting due diligence on third parties to confirm they have adequate security measures in place.
By prioritizing patient consent and ensuring responsible data sharing practices, private clinics can effectively address blood test privacy concerns and foster a culture of trust within the private healthcare sector.
Ensuring Accountability and Compliance in Private Healthcare
Accountability in data protection is paramount in the private healthcare sector, where organizations must remain vigilant in their compliance with UK data protection laws. Regulatory bodies such as the Information Commissioner’s Office (ICO) oversee compliance and can take enforcement actions against entities that fail to uphold data privacy standards.
Private clinics and laboratories are subject to regular inspections and audits, ensuring adherence to established data protection protocols. Non-compliance can lead to significant penalties, including fines and reputational damage.
Moreover, organizations must establish clear policies and procedures for managing data breaches, including immediate reporting mechanisms and remediation plans. This preparedness not only helps mitigate the impact of breaches but also reinforces accountability within the organization.
By maintaining a strong focus on accountability and compliance, the private healthcare sector can effectively address blood test privacy concerns and contribute to a safer and more secure healthcare environment for all patients.
Patient Rights and Access to Their Data in Private Healthcare
In the realm of private healthcare, patients retain the right to access their blood test data held by private sector entities. This right, enshrined in UK data protection laws, empowers patients to understand what information is retained about them and how it is used.
Patients can formally request access to their data, and private clinics must respond promptly, typically within one month. This process promotes transparency and enables patients to verify the accuracy of their data, ensuring compliance with the law regarding data processing.
Furthermore, patients are entitled to request corrections or amendments to their data if they identify inaccuracies. By exercising these rights, patients can help maintain the integrity of their health information and address any blood test privacy concerns they may have.
Emphasizing patient rights and access to data in the private sector is essential for fostering trust and ensuring that individuals feel informed and empowered regarding their health information.
Technological Innovations and Their Implications for Privacy in Healthcare
The rapid advancement of technology in healthcare has fundamentally transformed the management of patient data, including blood test data. However, these innovations also present unique challenges and opportunities related to privacy and data protection.
Revolutionizing Healthcare with Electronic Health Records
The widespread adoption of Electronic Health Records (EHRs) in the UK has redefined data accessibility for healthcare providers. EHRs facilitate seamless sharing of patient information across various healthcare settings, thereby enhancing the overall quality of care. Nevertheless, they also raise significant privacy concerns, particularly regarding the security of blood test data.
EHRs must be safeguarded with robust measures, including encryption and multi-factor authentication, to prevent unauthorized access. Healthcare organizations must ensure that their staff is adequately trained in data protection best practices, as human error frequently contributes to data breaches.
Moreover, patients need to be informed about how their data is stored and shared within EHR systems, reinforcing the importance of transparency and consent. By prioritizing the security of EHRs, healthcare providers can effectively address blood test privacy concerns while continuing to leverage the advantages of technology in patient care.
Leveraging AI for Enhanced Analysis of Blood Test Data
Artificial Intelligence (AI) is increasingly being utilized for the analysis of blood test data, improving the accuracy and efficiency of diagnoses. However, the integration of AI in healthcare must comply with UK privacy laws to effectively protect patient information.
AI systems must be designed with privacy considerations at the forefront, ensuring that patient data is anonymised and secured throughout the analysis process. Furthermore, healthcare providers must maintain transparency with patients regarding how AI is employed in their care, addressing any potential blood test privacy concerns.
By implementing ethical AI practices and prioritizing data protection, healthcare organizations can harness the benefits of AI while safeguarding patient privacy.
Exploring Blockchain Technology as a Solution for Enhanced Data Security
Blockchain technology is emerging as a promising solution for bolstering the security of blood test data in the UK. Its decentralized nature facilitates secure data storage and sharing, thereby reducing the risk of data breaches and unauthorized access.
By deploying blockchain, healthcare providers can ensure that patient data is immutable and traceable, offering an additional layer of security. This technology can facilitate secure data sharing among healthcare providers while maintaining patient confidentiality, thus addressing critical blood test privacy concerns.
As blockchain technology continues to evolve, its potential applications in healthcare data management could revolutionize how patient information is stored, shared, and protected, ultimately leading to a more secure healthcare ecosystem.
Addressing Biometric Data and Privacy Regulations in Healthcare
The utilization of biometric data, such as fingerprints and facial recognition, within healthcare settings must adhere to UK privacy regulations. While this technology can enhance security and improve patient identification, it also raises significant blood test privacy concerns.
Biometric data falls under the category of sensitive personal data according to UK law, necessitating stringent safeguards to protect individuals’ privacy. Healthcare providers must obtain explicit consent before collecting and processing biometric data and ensure that it is stored securely.
Moreover, patients should be informed about how their biometric data will be utilized and the measures in place to protect it. Transparent communication is crucial for addressing any privacy concerns associated with biometric data in healthcare.
By implementing robust privacy measures and maintaining transparency, healthcare organizations can effectively navigate the complexities of biometric data and safeguard patient privacy.
Ensuring Data Protection in Telemedicine Practices
The rise of telemedicine has transformed how patients access healthcare services, offering convenience and improved accessibility. However, telemedicine platforms must implement robust data protection measures to comply with UK privacy standards and ensure patient confidentiality.
Healthcare providers must employ end-to-end encryption and secure authentication protocols to protect blood test data exchanged during telemedicine consultations. Patients should be informed about the security measures in place and their rights regarding data protection.
Moreover, telemedicine platforms must adhere to strict guidelines on data storage and retention, ensuring that patient information is safeguarded throughout its lifecycle. By prioritizing data protection in telemedicine, healthcare providers can effectively address blood test privacy concerns while delivering high-quality care remotely.
Promoting Public Understanding and Education on Blood Test Privacy
Raising public awareness about blood test privacy concerns is essential for cultivating a culture of respect for patient data. Patients must be informed about their rights and the importance of data protection in healthcare.
The Critical Role of Patient Education in Data Privacy
Educating patients about their rights under UK data protection laws is vital for empowering them to make informed choices regarding their health information. Patients should be aware of their rights to access, rectify, and withdraw consent for their blood test data, ensuring they understand the control they have over their personal information.
Healthcare providers play a significant role in patient education, offering clear and accessible information regarding data protection measures and the implications of data sharing. Initiatives such as workshops, informational pamphlets, and online resources can greatly enhance patient understanding and engagement.
Additionally, fostering a culture of open dialogue surrounding data privacy is essential. Patients should feel comfortable asking questions and expressing concerns about their blood test privacy concerns, allowing healthcare providers to address any issues transparently and effectively.
By prioritizing patient education, healthcare organizations can promote a sense of ownership and responsibility regarding personal health data, ultimately leading to improved privacy outcomes and a more trusting patient-provider relationship.
Advocating for Enhanced Privacy Protections in Healthcare
Public advocacy for stronger privacy protections is essential in ensuring that blood test privacy concerns are taken seriously within the healthcare sector. Patients, healthcare professionals, and advocacy groups must collaborate to push for legislative reforms and improved data protection measures.
Engaging with policymakers and participating in public consultations can amplify the voices of individuals concerned about their data privacy. By advocating for stronger regulations and practices, stakeholders can drive meaningful change in the management of personal health information.
Moreover, raising awareness through social media campaigns and community outreach can help galvanize public support for privacy initiatives. Mobilizing communities around the significance of data protection can create a powerful movement advocating for patient rights and privacy.
Ultimately, cultivating a culture of advocacy for stronger privacy protections can lead to legislative reforms that prioritize blood test privacy concerns in the UK healthcare landscape, ensuring that patient rights are upheld and respected.
Frequently Asked Questions About Blood Test Privacy
What are the primary UK data protection laws governing blood tests?
The principal laws include the General Data Protection Regulation (GDPR) and the Data Protection Act 2018, which outline how personal health data, including blood tests, must be managed to ensure the protection of patient privacy.
How does GDPR affect the management of blood test data?
GDPR requires that healthcare providers obtain explicit consent from patients before processing their blood test data, while also ensuring patients have rights to access, rectify, and erase their information.
What rights do patients possess concerning their blood test data?
Patients have the right to access, correct, and withdraw consent for their blood test data under UK data protection laws, empowering them to effectively manage their health information.
What are the risks associated with data breaches in healthcare settings?
Data breaches can result in identity theft, medical fraud, and a decline in trust in healthcare providers, significantly jeopardizing patient well-being and overall healthcare outcomes.
How do UK hospitals prevent data breaches?
UK hospitals employ strategies such as encryption, access controls, and regular audits to safeguard patient data, alongside staff training on data protection best practices.
What constitutes informed consent in the healthcare context?
Informed consent requires that patients are fully aware of how their blood test data will be utilized and stored, enabling them to make informed decisions about their privacy and data management.
Can patients withdraw their consent for the use of their blood test data?
Yes, under UK law, patients are entitled to withdraw their consent for the use of their blood test data at any time, prompting healthcare providers to cease processing their data.
How does the NHS ensure the protection of patient data?
The NHS implements stringent data sharing policies and collaborates with NHS Digital to enhance data security measures, ensuring patient records are safeguarded and privacy concerns are adequately addressed.
What role does technology play in blood test data privacy?
Technology, including electronic health records and AI applications, can improve diagnostic accuracy but also raises privacy concerns, necessitating robust safeguards to protect patient data.
How can patients advocate for improved privacy protections?
Patients can advocate for stronger privacy protections by engaging with policymakers, participating in public consultations, and raising awareness through community outreach and social media initiatives.
Connect with us on Facebook!
This Article Was First Found On https://bloodtest.co.uk
The Article: Blood Test Privacy: Ensuring Data Protection Compliance appeared first on: https://ezbloodtest.com
The Article Blood Test Privacy: Safeguarding Your Data Compliance Was Found On https://limitsofstrategy.com
-

Blood Test Privacy Rights: Essential Insights to Understand
Understanding Your Rights: Comprehensive Overview of Blood Test Privacy Protections
Your Ultimate Resource for Navigating Privacy Rights in Blood Testing

Blood test privacy rights are essential for individuals undergoing various medical assessments, ensuring that their sensitive health information remains confidential and protected from unauthorized access and potential misuse. The legal framework that supports these rights is composed of multiple laws and regulations designed to maintain the confidentiality and security of personal health data. This legal structure is critical in fostering trust within the healthcare system, as patients feel more at ease knowing their private information is safeguarded and treated with the utmost respect and care.
In the UK, a key pillar of this protective framework is the Data Protection Act 2018, which significantly contributes to securing personal data, including medical records. This legislation empowers individuals by providing them with the right to access information regarding how their data is collected, utilized, and shared with third parties. Additionally, the General Data Protection Regulation (GDPR) complements these rights by granting individuals greater control over their personal information, allowing them to access and correct inaccuracies. By familiarizing themselves with these vital legal provisions, patients can effectively advocate for their rights and ensure their privacy is thoroughly protected.
Moreover, the NHS has established strict guidelines to uphold patient confidentiality throughout the blood testing process. From the initial sample collection to the analysis of results, every step is meticulously crafted with rigorous protocols aimed at safeguarding personal information. The NHS’s steadfast commitment to preserving blood test privacy rights plays a crucial role in instilling confidence in patients seeking medical care, assuring them that their sensitive information is both secure and protected.
The Vital Role of Blood Test Privacy: Recognizing Its Importance for Patients
Ensuring privacy during medical testing goes beyond mere legal compliance; it is a fundamental aspect of nurturing patient trust and dignity. Individuals undergoing blood tests frequently share highly sensitive health information that may include potential diagnoses and other personal details. The importance of blood test privacy rights becomes particularly significant in this context, as breaches can result in emotional distress, discrimination, or social stigma, all of which can have lasting effects on individuals and their families.
Furthermore, the relationship between healthcare providers and patients is inherently built on trust. When patients are confident that their private information will remain confidential, they are more likely to seek medical assistance and share critical health information that could significantly influence their treatment plans. Conversely, a lack of privacy can discourage individuals from accessing necessary healthcare services, ultimately leading to adverse health outcomes and complications that could have been avoided.
The broader societal implications of blood test privacy rights are profound and wide-ranging. Protecting personal health data fosters a culture of respect for individual autonomy and promotes a more engaged and responsible public approach to health-related matters. This cultural shift is essential for advancing public health initiatives and ensuring that individuals feel secure in managing their health and overall well-being.
Key Legislation: Important Acts and Regulations Every Patient Must Know
A variety of essential legislative measures form the foundation of blood test privacy rights and provide critical protections for patients. The Data Protection Act 2018 is a fundamental aspect of the GDPR, ensuring that personal data is processed lawfully and transparently. This Act delineates individuals’ rights concerning their health information and the responsibilities of those who manage that data, thereby empowering patients to take charge of their personal data.
Another crucial piece of legislation is the Access to Health Records Act 1990, which grants individuals the right to access their health records, including blood test results. Such access is vital for patients who aim to deepen their understanding of their care and make informed decisions regarding their health. This Act promotes transparency and accountability within the healthcare system, reinforcing the principle that individuals possess the right to control their health information.
Additionally, the NHS Code of Practice on Confidentiality provides essential guidance on managing patient information. This code emphasizes the necessity of obtaining patient consent and specifies that personal health data should only be shared with third parties when absolutely necessary and with the patient’s explicit permission. Understanding these foundational legislative frameworks equips patients to effectively advocate for their blood test privacy rights and ensures their information is adequately safeguarded.
Empowering Yourself: Proactive Measures to Assert Your Privacy Rights

Steps to Effectively Request Access to Your Blood Test Results
Accessing your blood test results is not only a right; it serves as a vital step to empower you in managing your health and well-being. To navigate this process successfully, it is essential to understand the specific steps involved. Begin by reaching out to the healthcare provider or laboratory that conducted the test. Most institutions have established clear protocols for patients to request their results, often requiring the completion of a consent form in line with blood test privacy rights.
Once your request has been submitted, it is crucial to be aware of the expected response time. Healthcare providers are typically obligated to respond to requests within a specified timeframe, usually within 30 days. If you experience any delays or lack of communication, do not hesitate to follow up to confirm that your request is being processed. This proactive approach not only keeps you informed but also demonstrates your commitment to maintaining your health and rights.
Additionally, consider requesting your results in a format that is easily accessible and understandable to you. Many healthcare providers now offer digital access to results through secure online portals, which adds an extra layer of convenience and security. By utilizing these digital platforms, you can maintain greater control over your information while ensuring that your blood test privacy rights are respected and upheld throughout the entire process.
Best Practices for Protecting Your Health Data
As awareness of blood test privacy rights continues to rise, it becomes increasingly crucial for individuals to adopt best practices for safeguarding their personal health information. One of the most effective strategies is to remain vigilant about where and how your data is shared. Always inquire about the privacy policies of healthcare providers, laboratories, and testing services to gain a clear understanding of their data handling practices and protocols.
When interacting with data-handling healthcare providers, utilize secure messaging systems or encrypted email services to minimize the risk of unauthorized access to your sensitive information. Avoid sharing personal health data over unsecured channels, such as social media or unencrypted emails, as these can expose your information to potential breaches and misuse. Taking these precautions can significantly enhance your data security and privacy.
Moreover, it is vital to remain conscious of your digital footprint. If you are engaging with online health services, ensure that the platform complies with relevant privacy regulations and employs robust security measures. Look for indicators of encryption and data protection certifications before sharing any personal information. By adopting these practices, you can significantly boost your protection and ensure that your blood test privacy rights are thoroughly maintained and respected.
What to Do If Your Privacy Is Breached

In the unfortunate event that your blood test results are compromised, it is essential to take swift and decisive action. First, assess the nature of the breach—determine whether it was due to accidental exposure or a deliberate act. This understanding will guide your subsequent actions and inform the appropriate response to the situation.
If you suspect that your blood test privacy has been violated, contact the organization responsible for the breach immediately. They are legally obligated to inform you of the incident, and reporting it ensures that necessary measures are taken to mitigate any further risks. Additionally, consider filing a complaint with the Information Commissioner’s Office (ICO) if you believe your rights have been infringed upon. The ICO can investigate the incident and take appropriate action against organizations that fail to uphold data protection standards.
Finally, continuously monitor your health information and personal accounts for any unusual activity that may indicate data misuse. This vigilance can help you detect potential issues early on. Being informed about your rights and the steps to take in the event of a breach not only empowers you but also enhances your ability to effectively advocate among healthcare providers regarding your blood test privacy rights.
Expert Insights on Blood Test Privacy Rights
Legal Perspectives on Safeguarding Patient Privacy Rights
We consulted with several legal professionals specializing in medical privacy laws to deepen our understanding of blood test privacy rights. Their insights illuminate the complexities and nuances involved in protecting patient data. A prominent solicitor emphasized that while legislation surrounding patient data protection is robust, the rapid advancement of technology often outpaces regulatory measures, creating gaps in protection that patients must navigate carefully.
Experts highlight the critical importance of patient education and awareness regarding their health data rights, as this understanding can help individuals avoid potential breaches. As one legal advisor articulated, “Knowledge is power. Patients who understand their rights are better equipped to protect themselves and challenge any infringements.”
Furthermore, professionals stress that healthcare institutions must invest in training their staff on data protection laws and ethical responsibilities. Such training not only safeguards patient information but also fosters a culture of respect and accountability within healthcare organizations. By engaging with these experts, patients can gain invaluable insights into effectively navigating the complexities of blood test privacy rights and protecting their sensitive information.
Case Studies Illustrating Privacy Challenges in Healthcare
Examining real-world case studies provides critical insights into the significance of blood test privacy rights. One notable case involved a major laboratory chain that inadvertently exposed thousands of patients’ blood test results due to a software vulnerability. This incident raised substantial concerns regarding the adequacy of data protection measures within healthcare systems and the potential repercussions for affected individuals.
This case underscores the necessity for healthcare providers to implement effective measures and conduct regular audits of their systems to identify and rectify vulnerabilities. It also highlights the importance of transparency with patients. Following the breach, the laboratory faced backlash from patients who felt their trust had been violated, emphasizing the need for effective communication and prompt action to maintain patient confidence in their healthcare providers.
Another case featured a small clinic that failed to securely store patient records, resulting in unauthorized access to sensitive information. The clinic faced legal repercussions, serving as a stark reminder of the potential consequences of neglecting blood test privacy rights. These case studies illustrate the urgent need for healthcare providers to prioritize data protection and uphold patients’ rights to maintain their trust in the system.
Future Trends in Blood Test Privacy Rights
As technology continues to evolve, the landscape of privacy rights is poised for significant transformation. Experts predict that the rise of telemedicine and digital health services will necessitate the introduction of new regulations to address the unique challenges presented by remote healthcare. Ensuring that patient data remains secure in a digital environment will be essential as more individuals turn to online platforms for health management and consultations.
Additionally, the integration of artificial intelligence in healthcare introduces both opportunities and challenges. While AI can enhance diagnostic accuracy and streamline processes, it also raises significant concerns regarding data security and patient privacy. Future regulations must be developed to address these issues, ensuring that innovations do not compromise blood test privacy rights or the integrity of patient data.
Moreover, there is a growing trend towards patient empowerment in managing health data. Patients increasingly seek control over their health information, resulting in heightened demands for transparency from healthcare providers. As this trend continues to evolve, organizations will need to adapt to meet the changing expectations of patients, furthering the understanding of Blood Test Privacy Rights: Essential Considerations for Employers.
Workplace Blood Testing: Balancing Employee Privacy and Safety Needs
In the context of workplace testing, employers face the challenge of balancing employee safety with the necessity of preserving blood test privacy rights. Conducting blood tests within the workplace can serve as a valuable tool for ensuring employee health and safety; however, this must be approached with caution to avoid infringing upon employees’ rights.
Employers should establish clear policies regarding workplace blood testing, detailing the reasons for testing, the types of tests conducted, and the measures implemented to protect employee privacy. Effective communication is paramount; employees should be informed about how their test results will be utilized and who will have access to this sensitive information. Transparency fosters trust and can alleviate concerns employees may have regarding the potential misuse of their data.
Moreover, it is equally important for employers to obtain informed consent from employees before conducting blood tests. This consent should clearly define the scope of testing, the rationale behind it, and the privacy measures established to protect individual rights, thereby prioritizing blood test privacy in the workplace and ensuring that employees feel comfortable and informed throughout the process.
Understanding Legal Responsibilities: Essential Knowledge for Employers
Employers must possess a comprehensive understanding of their legal obligations concerning blood test privacy rights. The Data Protection Act 2018 imposes stringent requirements on how employers collect, process, and store employee health data. Employers must ensure that any conducted blood tests are relevant to health and safety considerations and justified accordingly to uphold the rights of their employees.
Furthermore, employers need to establish comprehensive data policies detailing how employee health information will be managed and safeguarded. Conducting training sessions for HR personnel and management on data protection laws is vital to ensure compliance and mitigate risks associated with mishandling sensitive information.
In the event of a data breach, employers are required to report the incident to the ICO within 72 hours if it poses a risk to employees’ rights. Understanding these legal obligations not only protects employees but also safeguards employers from potential legal repercussions associated with violations of blood test privacy rights and other privacy-related laws.
Employees benefit from a range of protections regarding various privacy rights in the workplace. Understanding these rights empowers individuals to advocate for themselves and ensure their personal health information is protected. A fundamental right is informed consent; employees must be informed about the purpose of any blood tests and how their results will be managed in a way that respects their privacy.
Additionally, employees have the right to access their test results and comprehend their implications fully. Employers must provide clear channels for employees to request this information and ensure it is delivered securely and confidentially. If an employee suspects that their privacy has been compromised, they have the right to report the issue to their HR department or the ICO.
Furthermore, employees are protected against discrimination based on health information obtained from blood tests. Employers must not utilize this information to make employment decisions, such as hiring, promotion, or termination, unless it directly relates to job performance. Understanding these rights is crucial for employees to effectively navigate the intricacies of blood test privacy rights in the workplace and ensure their voices are heard.
Comprehensive Overview of Healthcare Providers’ Responsibilities in Privacy Protection
Ethical Duties: Upholding Standards of Patient Privacy
Healthcare providers bear a significant ethical responsibility to uphold blood test privacy rights. Patients place their trust in healthcare professionals, expecting that their blood tests will be conducted with an assurance that sensitive health information will be treated with the utmost confidentiality and respect. This ethical obligation extends beyond mere legal compliance; it reflects a profound commitment to safeguarding patient dignity and fostering a respectful healthcare environment.
To fulfill this responsibility, healthcare providers must implement robust data protection measures, including secure storage and transmission of patient information. This encompasses the use of encryption for electronic records and ensuring that physical records are stored securely. Additionally, comprehensive staff training on patient confidentiality is crucial for fostering a culture of respect for blood test privacy rights and ensuring that all staff members understand the importance of safeguarding sensitive information.
Moreover, providers should communicate transparently about how patient data will be utilized and shared. By educating patients about their rights and the measures in place to safeguard their information, healthcare providers can enhance patient trust and encourage open dialogue, ultimately leading to improved health outcomes and patient satisfaction.
Ensuring Regulatory Compliance: Adhering to Privacy Protection Standards
Compliance with regulations governing blood test privacy rights is paramount for healthcare providers. The Data Protection Act 2018 and GDPR establish clear guidelines surrounding the collection, storage, and processing of patient data, necessitating that healthcare providers obtain informed consent from patients before conducting blood tests. This process must clearly articulate the purpose and potential uses of the data collected to ensure that patients are fully informed.
Additionally, healthcare providers must maintain accurate records of patient consent and regularly review their data protection policies to ensure compliance with evolving regulations. Conducting routine audits of data-handling practices can help identify vulnerabilities and areas for improvement in safeguarding patient information.
In the event of a data breach, healthcare providers are required to promptly notify affected patients and the ICO. Understanding these obligations and implementing robust compliance measures not only protects patient data but also preserves the reputation of healthcare institutions and their commitment to optimal privacy protection and ethical standards.
Effective training of healthcare staff is critical for upholding blood test privacy rights. Training programs should cover legal obligations surrounding data protection, ethical considerations, and best practices for maintaining patient confidentiality. Staff should be educated on the importance of safeguarding patient data and the potential ramifications of mishandling it, creating a culture of accountability and respect within healthcare settings.
Furthermore, healthcare providers should establish clear protocols for managing patient data, including guidelines for sharing information with third parties. By equipping staff with the necessary knowledge and tools to protect blood test privacy rights, healthcare institutions can enhance patient trust and improve overall care quality.
Addressing Common Concerns Regarding Blood Test Privacy Rights
Can My Insurance Provider Access My Blood Test Results? Understanding Your Rights
A prevalent concern among patients is whether their insurance provider can access their blood test results. Generally, insurance companies may request access to specific health information, including blood test results, but only with the patient’s explicit consent. Patients should be fully aware of their rights regarding this data and ensure they understand any consent forms they sign before allowing access.
Moreover, data protection laws dictate that insurance companies must handle personal health information with care and confidentiality. If you have concerns about your insurer accessing your blood test results, it is advisable to review your policy and engage in a discussion with a professional to clarify any uncertainties regarding your rights and protections.
What Happens to My Data After a Blood Test? Key Insights
After a blood test, your data management processes are designed to protect your blood test privacy rights. Typically, test results are securely stored within the healthcare provider’s systems, with access restricted to authorized personnel only. Data may be retained for a specific duration, after which it may be anonymized or securely disposed of in accordance with relevant regulations.
Patients have the right to inquire about the storage and handling of their test results, and healthcare providers should provide clear information regarding their data retention policies. Understanding the lifecycle of blood test data is essential to ensuring that patients’ rights are upheld throughout the process, promoting transparency and trust in the healthcare system.
How to Protect Patient Privacy When Using Online Testing Services
With the increasing popularity of online testing services, patients must take proactive measures to protect their blood test privacy. Before utilizing any online service, research the provider’s privacy policies and verify compliance with relevant data protection regulations. Look for services that implement encryption and employ secure data handling practices to safeguard your information effectively.
Additionally, consider implementing strong passwords and two-factor authentication for online accounts related to your health data. Being cautious about the information you share online and regularly reviewing your privacy settings can significantly enhance your protection when utilizing digital health services, ensuring your personal information remains confidential and secure.
Frequently Asked Questions About Blood Test Privacy Rights
What rights do I have regarding my blood test results?
You have the right to access your blood test results, understand how your data is utilized, and request necessary corrections to any inaccuracies that may exist.
Can my employer conduct blood tests?
Employers can conduct blood tests, but they must obtain informed consent and ensure that employee privacy is upheld throughout the process to protect their rights and dignity.
What should I do if I suspect a privacy breach?
Immediately report the suspected breach to the relevant healthcare provider and consider filing a complaint with the Information Commissioner’s Office (ICO) if necessary to address the issue appropriately.
How long are blood test results stored?
Blood test results are typically stored for a specific duration according to healthcare regulations, after which they may be securely disposed of to protect patient privacy.
Can I refuse a blood test at work?
Yes, you can refuse a blood test at work; however, it’s essential to understand the implications this refusal may have if the test is mandated for safety reasons or company policies.
Do I have control over who sees my health data?
Yes, you have the right to control access to your health data and can grant or revoke consent for sharing information with third parties, ensuring your privacy is respected.
What happens if my blood test results are shared without consent?
If your blood test results are shared without your consent, this may constitute a breach of your privacy rights, and you should consider reporting the incident to the ICO for further investigation.
Can I access my child’s blood test results?
As a parent or guardian, you generally have the right to access your child’s blood test results, subject to specific regulations and consent requirements that may apply.
How can I ensure my data is protected when using online services?
To protect your data when using online services, research the provider’s privacy policies, utilize strong passwords, and enable two-factor authentication for added security and protection of your personal information.
What should I do if I don’t understand my test results?
If you find your test results confusing, consult with your healthcare provider for information and guidance on any necessary next steps to better understand your health and the implications of your results.
Connect with us on Facebook!
This Article Was First Found On https://bloodtest.co.uk
The Article: Blood Test Privacy Rights: Essential Insights for Everyone appeared first on: https://ezbloodtest.com
The Article Blood Test Privacy Rights: Key Insights You Should Know Was Found On https://limitsofstrategy.com